Adrian Kingsley-Hughes/ZDNET ZDNET’s key takeaways I tested a 20-in-1 gadget cleaning tool, which is available from Amazon for $12. The kit is compact, the components are all quality items that can be reused many times, and the kit contains a variety of brushes and cleaners. A larger container for lens cleaning fluid would have been […]
Cloud Console Cartographer is an open-source tool that maps noisy log activity into highly consolidated, succinct events to help security practitioners cut through the noise and understand console behavior in their environment. “Infrastructure as code has replaced a lot of the need for console access for many organizations, but there are still plenty of instances […]
The simplified version of this python tool is available here. IOC FileName SHA256 vcruntime140.dll 72b92683052e0c813890caf7b4f8bfd331a8b2afc324dd545d46138f677178c4 d0a8fa332950b72968bdd1c8a1a0824dd479220d044e8c89a7dea4434b741750 YARA Rule: import “pe”rule possible_wine_loader_export_function {meta:author = “@tccontre18 – Br3akp0int”description = “possible wine loader export function setup code”date = “2024-04-03″sha256 = “72b92683052e0c813890caf7b4f8bfd331a8b2afc324dd545d46138f677178c4″strings:$exp_loader = {48 83 EC 08 48 8D 0D ?? ?? ?? ?? 48 C7 C2 28 80 00 […]
The Open Source Security Foundation (OpenSSF), in collaboration with the US government, has launched a new tool to simplify Software Bill of Materials (SBOMs) management for organizations. Protobom, the new open source software tool, will help all organizations read and generate SBOMs and file data, as well as translate this data across standard industry SBOM […]
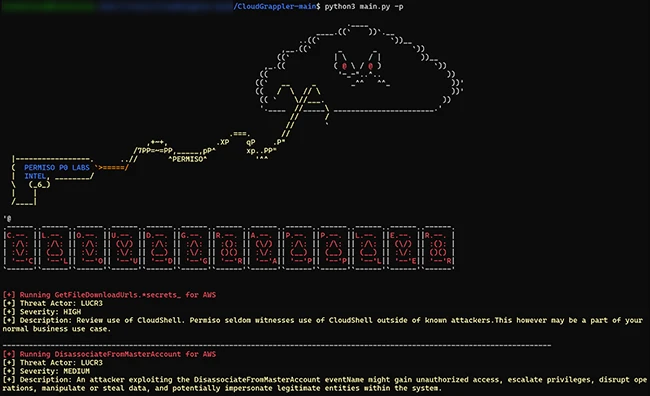
CloudGrappler is an open-source tool designed to assist security teams in identifying threat actors within their AWS and Azure environments. The tool, built on the foundation of Cado Security’s cloudgrep project, offers enhanced detection capabilities based on the tactics, techniques, and procedures (TTPs) of modern cloud threat actors like LUCR-3 (Scattered Spider). CloudGrappler queries for […]
A popular tool used by numerous state and local governments to manage public records requests contained defects that could have allowed hackers to download troves of unsecured files tethered to records inquiries, including highly sensitive personal information like IDs, fingerprints, child welfare documentation and medical reports, Nextgov/FCW has learned. The flaws, which have been remedied, […]
RiskInDroid (Risk Index for Android) is an open-source tool for quantitative risk analysis of Android applications based on machine learning techniques. How RiskInDroid works “A user should be able to quickly assess an application’s level of risk by simply glancing at RiskInDroid’s output, and they should be able to compare the app’s risk with others […]
Threat actors used the open-source hypervisor QEMU as a network tunneling tool to create a covert communication channel, demonstrating the diverse methods attackers use to remain stealthy.
SiCat is an open-source tool for exploit research designed to source and compile information about exploits from open channels and internal databases. Its primary aim is to assist in cybersecurity, enabling users to search the internet for potential vulnerabilities and corresponding exploits. Akas Wisnu Aji, the creator of SiCat, outlined the key features of the […]