Apr 26, 2024NewsroomThreat Intelligence / Cyber Attack Threat actors are attempting to actively exploit a critical security flaw in the WP‑Automatic plugin for WordPress that could allow site takeovers. The shortcoming, tracked as CVE-2024-27956, carries a CVSS score of 9.9 out of a maximum of 10. It impacts all versions of the plugin prior to […]
How It Works The sequence begins with threat actors creating a fake site on a web hosting service, which remains undetected by the hosting service itself. When a user searches for relevant information and clicks on a link from the search results, they unknowingly access the malicious site. Interestingly, if the user directly enters the […]
A GitHub flaw, or possibly a design decision, is being abused by threat actors to distribute malware using URLs associated with Microsoft repositories, making the files appear trustworthy.
Threat actors created a website to impersonate UsenetClub, a subscription service for “uncensored” access to images and videos downloaded from Usenet. They claimed to provide free access to the site after the installation of a “CryptVPN” software.
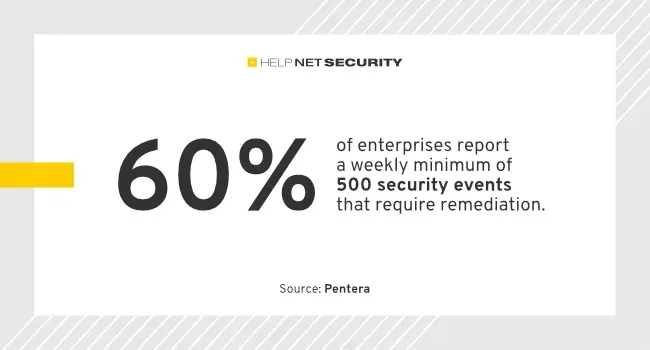
Threat actors are continuing to successfully breach across the entire attack surface and the stakes are only getting higher: 93% of enterprises who admitted a breach reported unplanned downtime, data exposure, or financial loss as a result, according to Pentera. Pentera surveyed 450 CISOs, CIOs, and IT security leaders at enterprise companies with more than […]
Between crossovers – Do threat actors play dirty or desperate? In our dataset of over 11,000 victim organizations that have experienced a Cyber Extortion / Ransomware attack, we noticed that some victims re-occur. Consequently, the question arises why we observe a re-victimization and whether or not this is an actual second attack, an affiliate crossover […]
Threat actors behind the Akira ransomware group have extorted approximately $42 million in illicit proceeds after breaching the networks of more than 250 victims as of January 1, 2024. “Since March 2023, Akira ransomware has impacted a wide range of businesses and critical infrastructure entities in North America, Europe, and Australia,” cybersecurity agencies from the […]
Apr 18, 2024NewsroomContainer Security / Cryptocurrency Threat actors are actively exploiting critical vulnerabilities in OpenMetadata to gain unauthorized access to Kubernetes workloads and leverage them for cryptocurrency mining activity. That’s according to the Microsoft Threat Intelligence team, which said the flaws have been weaponized since the start of April 2024. OpenMetadata is an open-source platform […]
Apr 17, 2024NewsroomEncryption / Vulnerability Threat actors are exploiting unpatched Atlassian servers to deploy a Linux variant of Cerber (aka C3RB3R) ransomware. The attacks leverage CVE-2023-22518 (CVSS score: 9.1), a critical security vulnerability impacting the Atlassian Confluence Data Center and Server that allows an unauthenticated attacker to reset Confluence and create an administrator account. Armed […]