Apr 27, 2024NewsroomCyber Attack / Malware Cybersecurity researchers have discovered a targeted operation against Ukraine that has been found leveraging a nearly seven-year-old flaw in Microsoft Office to deliver Cobalt Strike on compromised systems. The attack chain, which took place at the end of 2023 according to Deep Instinct, employs a PowerPoint slideshow file (“signal-2023-12-20-160512.ppsx”) […]
Microsoft It’s no joke. Microsoft and IBM have joined forces to open-source the 1988 operating system MS-DOS 4.0 under the MIT License. Why? Well, why not? As Scott Hanselman, Microsoft’s VP of the developer community, and Jeff Wilcox, head of Microsoft’s Open Source Programs Office, recount in Microsoft’s Open Source Blog, “a young English researcher […]
In Recent years, Netflix and Apple TV+ have been duking it out to have the most prestigious film offerings, but some of the best movies are on Amazon Prime Video. The streamer was one of the first to go around picking up film festival darlings and other lovable favorites, and they’re all still there in […]
akinbostanci/Getty Images Modern professionals have busy workloads and juggling all these demands is tough, especially when unexpected challenges appear on the horizon. Research suggests more than half (57%) of IT managers have to manage more incidents than they can handle. Also: 5 ways to manage your time more effectively at work If you don’t manage […]
I’ll scream it from the mountaintops as many times as I have to: Your bedroom should have a bottle of lube! Ideally more than one. Whether you’re flying solo or with a copilot(s), too much friction is a bad time for everyone. Even if it doesn’t seem like you need a lubricant, you’d be better […]
Here are a few tips we have learned from using Govee smart lighting for the past few years. Installation: Plan installations carefully, particularly with panels, by testing your intended layout before you stick anything to the wall. In particular, think about where the power cord will end up. Clean any surface you intend to stick […]
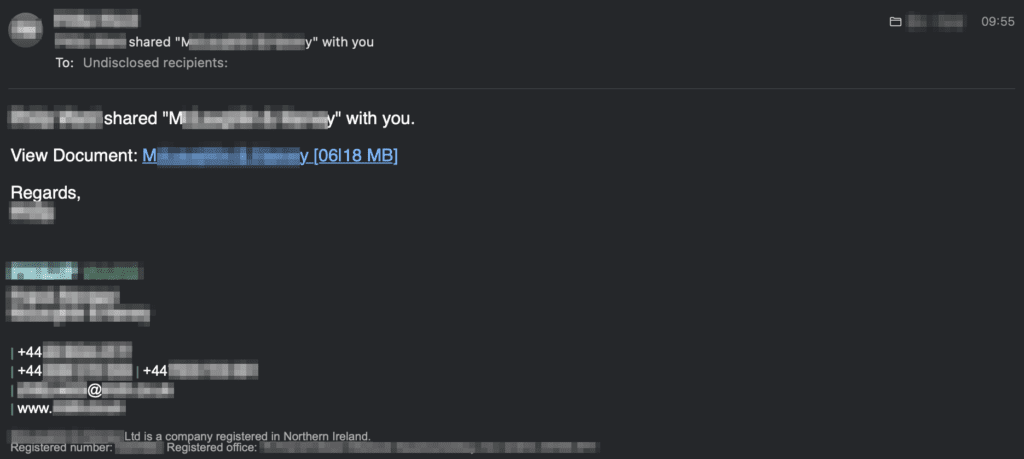
Autodesk is hosting malicious PDF files that lead phishing attack victims to have their Microsoft login credentials stolen. The elaborate phishing campaign behind these attacks is much more convincing than normal, as it uses compromised email accounts to find and attack new targets. These accounts are used to send phishing emails to existing contacts, using […]
Researchers have sinkholed a command and control server for a variant of the PlugX malware and observed in six months more than 2.5 million connections from unique IP addresses.
There’s a strong chance we will see Nintendo’s next-generation console in 2025, but if you just have been itching to play some Nintendo games, the Switch remains an excellent buy. You’re in luck because Amazon is offering $25 off when you clip the on-page coupon, dropping the price to $324. Not only is this a […]