Security researchers have stopped a “credible” takeover attempt reminiscent of the recent XZ Utils backdoor incident — further highlighting the urgent need to address weaknesses in the management of open source software. Researchers at the OpenJS Foundation — which monitors JavaScript projects used by billions of websites worldwide — said Monday that they “received a […]
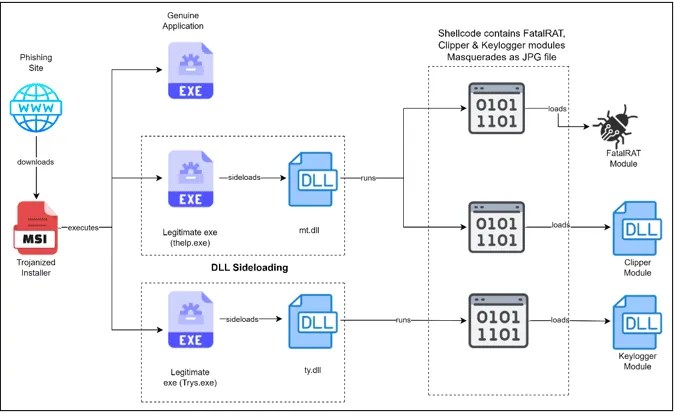
Researchers have discovered a sophisticated phishing campaign meticulously crafted to target cryptocurrency users. This elaborate scheme, equipped with the notorious FatalRAT along with supplementary malware like Clipper and Keylogger, was orchestrated by threat actors utilizing DLL side-loading techniques. Source: Infection Chain (Cyble) FatalRAT, renowned as a Remote Access Trojan, grants attackers control over victim systems, […]
Apr 15, 2024NewsroomSpyware / Mobile Security Cybersecurity researchers have discovered a “renewed” cyber espionage campaign targeting users in South Asia with the aim of delivering an Apple iOS spyware implant called LightSpy. “The latest iteration of LightSpy, dubbed ‘F_Warehouse,’ boasts a modular framework with extensive spying features,” the BlackBerry Threat Research and Intelligence Team said […]
Apr 12, 2024NewsroomWeb Security / WordPress Cybersecurity researchers have discovered a credit card skimmer that’s concealed within a fake Meta Pixel tracker script in an attempt to evade detection. Sucuri said that the malware is injected into websites through tools that allow for custom code, such as WordPress plugins like Simple Custom CSS and JS […]
Researchers have demonstrated the “first native Spectre v2 exploit” for a new speculative execution side-channel flaw that impacts Linux systems running on many modern Intel processors.
Apr 10, 2024NewsroomCyber Crime / Malvertising Cybersecurity researchers have discovered a new Raspberry Robin campaign wave that propagates the malware through malicious Windows Script Files (WSFs) since March 2024. “Historically, Raspberry Robin was known to spread through removable media like USB drives, but over time its distributors have experimented with other initial infection vectors,” HP […]
Cybersecurity researchers from Bitdefender discovered critical vulnerabilities in LG TVs running webOS versions 4 through 7. These vulnerabilities could allow attackers to gain complete control over the TV, steal data, or install malware. The vulnerabilities were identified by Bitdefender as part of their research into the security of popular IoT devices. They found that attackers […]
Apr 10, 2024NewsroomHardware Security / Linux Cybersecurity researchers have disclosed what they say is the “first native Spectre v2 exploit” against the Linux kernel on Intel systems that could be exploited to read sensitive data from the memory. The exploit, called Native Branch History Injection (BHI), can be used to leak arbitrary kernel memory at […]
Cybersecurity researchers have discovered an intricate multi-stage attack that leverages invoice-themed phishing decoys to deliver a wide range of malware such as Venom RAT, Remcos RAT, XWorm, NanoCore RAT, and a stealer that targets crypto wallets.