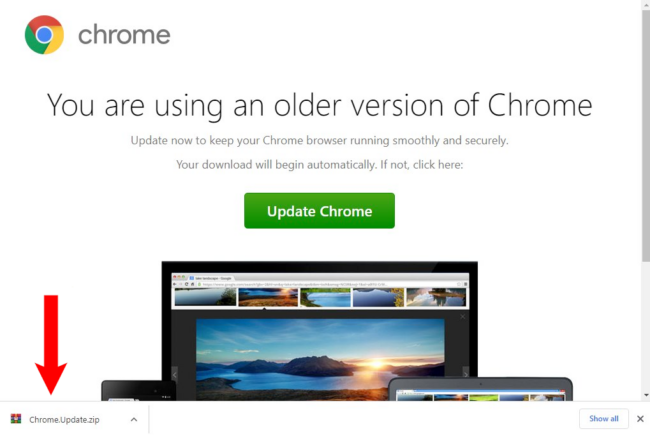
SocGholish malware, otherwise known as “fake browser updates”, is one of the most common types of malware infections that we see on hacked websites. This long-standing malware campaign leverages a JavaScript malware framework that has been in use since at least 2017. The malware attempts to trick unsuspecting users into downloading what is actually a […]
Feb 29, 2024NewsroomLinux / Network Security Threat hunters have discovered a new Linux malware called GTPDOOR that’s designed to be deployed in telecom networks that are adjacent to GPRS roaming exchanges (GRX) The malware is novel in the fact that it leverages the GPRS Tunnelling Protocol (GTP) for command-and-control (C2) communications. GPRS roaming allows subscribers […]
Security researchers have encountered a new cryptojacking campaign that uses a new piece of malware called Migo that targets Redis servers on Linux hosts. The campaign came to light after Cado Security researchers noticed new commands exploiting Redis systems in the wild. Initial access According to Cado security, Migo is distributed as a Golang ELF […]
Feb 14, 2024NewsroomMalware / Cybercrime The infamous malware loader and initial access broker known as Bumblebee has resurfaced after a four-month absence as part of a new phishing campaign observed in February 2024. Enterprise security firm Proofpoint said the activity targets organizations in the U.S. with voicemail-themed lures containing links to OneDrive URLs. “The URLs […]
Malware designed to seek out and disable enterprise security defenses has surged in popularity over the past year to comprise nearly a quarter (26%) of all detections in 2023, according to Picus Security. The cybersecurity vendor revealed the news in its Picus Red Report 2024, compiled from analysis of 612,080 malicious files last year, to […]
Bumblebee malware has re-emerged following a four-month absence from the cyber threat landscape, according to Proofpoint research. The new campaign, observed in February 2024, used a “significantly different” attack chain compared to previous Bumblebee infiltrations. The return of Bumblebee coincides with the reappearance of several notorious threat actors at the start of 2024 following a […]
Feb 13, 2024NewsroomCyber Threat / Malware The threat actors behind the PikaBot malware have made significant changes to the malware in what has been described as a case of “devolution.” “Although it appears to be in a new development cycle and testing phase, the developers have reduced the complexity of the code by removing advanced […]
Cybercrime , Fraud Management & Cybercrime , Malware as-a-Service 2 Men Arrested in Malta, Nigeria for Hawking Malware on Hacking Forums Since 2012 Cal Harrison • February 9, 2024 Image: Shutterstock Federal authorities have seized internet domains and arrested two men in Malta and Nigeria who they say served as sales and customer […]
Feb 10, 2024NewsroommacOS Malware / Cyber Threat Apple macOS users are the target of a new Rust-based backdoor that has been operating under the radar since November 2023. The backdoor, codenamed RustDoor by Bitdefender, has been found to impersonate an update for Microsoft Visual Studio and target both Intel and Arm architectures. The exact initial […]