A data breach that impacted car manufacturer Tesla in May of this year has been confirmed as the result of “insider wrongdoing”, according to a data breach notice filed by the company. The data breach was discovered in May after German publication Handelsplatt broke the news of the cyber security incident, which saw 100GB worth […]
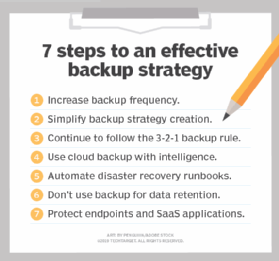
What is off-site backup? Off-site backup is a method of backing up data to a remote server or to media that’s transported off site. The two most common forms of off-site backup are cloud backup and tape backup. During cloud backup, also referred to as online backup, a copy of the data is sent over […]
Cyber Security Hub takes a look at the top cyber attacks, data breaches and cyber security incidents across the globe that happened in June, 2023. Contents: MOVEit cyber attack impacts multiple businesses A cyber attack on document transfer service MOVEit led to a series of data breaches of high-profile companies including PricewaterhouseCooper (PwC), Ernst and […]
Here, Cyber Security Hub takes a look at the top cyber attacks, data breaches and cyber security incidents across the globe that happened in July, 2023. Contents: Hackers steal $20 million from Revolut Fanfiction site targeted by DDoS attack Microsoft hack sees emails stolen from US agencies HCA Healthcare data breach […]
Discord.io, a custom invite service for the instant messaging service Discord, has suffered a data breach that exposed the personal data of more that 760,000 users. Discord.io is a third-party service which allows Discord users to create customized invitations to their channels on Discord itself. The breach was discovered on August 14, after a […]
Two UK police forces have admitted to a data breach caused by a “technical error” that saw the personally identifying information of victims, witnesses and suspects mistakenly posted online following Freedom of Information (FOI) requests. Norfolk and Suffolk police admitted on August 15 that the data of 1,230 people was included in files published to […]
Companies of all sizes are being challenged to install policies and secure data on a growing number of devices, which leads to an increased volume of alerts to be managed. All this, while balancing the skills and resources gap in IT and cyber security. CISOs and security owners, especially those operating small and medium sized […]
Companies rely on data transfers to communicate between departments and with clients. However, there are several risks if these data transfers are insecure. If insecure file transfer methods such as unencrypted email or cloud services are used, companies can open themselves up to potential exploitation by malicious actors. When considering data transfer security, one of […]
What is a unified computing system (UCS)? A unified computing system (UCS) is a converged data center architecture that integrates computing, networking and storage resources to increase efficiency and enable centralized management. UCS products are designed and configured to work together effectively. The goal of a UCS product line is to simplify the number of […]