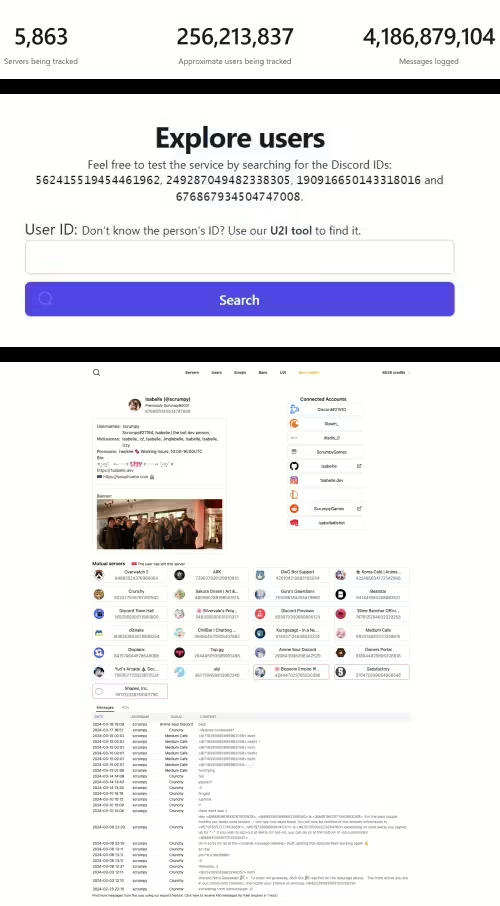
Apr 28, 2024NewsroomCredential Stuffing / Data Breach Identity and access management (IAM) services provider Okta has warned of a spike in the “frequency and scale” of credential stuffing attacks aimed at online services. These unprecedented attacks, observed over the last month, are said to be facilitated by “the broad availability of residential proxy services, lists […]
Your Android phone‘s web browser picks up a lot of data from all of the websites that you visit, and a lot of that does not need to be on your phone. Whether you’re using Google Chrome, Mozilla Firefox or Samsung Internet, this data stored in your cookies and cache can be helpful in some cases. […]
One in five UK companies has had potentially sensitive corporate data exposed via employee use of generative AI (GenAI), a new report has revealed. London-headquartered cybersecurity services provider RiverSafe polled 250 CISOs nationwide to compile its new report, Underfunded and Under Reported: Threats, Breaches, and Budgets. The data leak risks of unmanaged GenAI use help […]
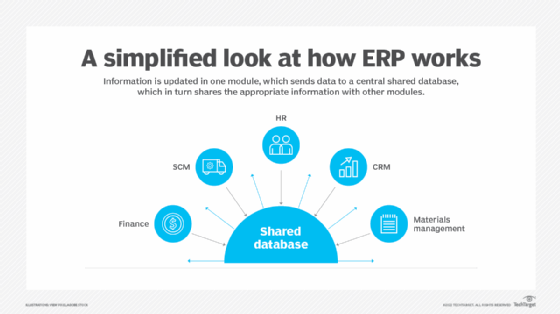
What is Electronic Data Interchange (EDI)? Electronic Data Interchange (EDI) is the transfer of data from one computer system to another by standardized message formatting without the need for human intervention. The goal of EDI is to replace manual processes that involve the exchange of documents with a fully autonomous one. EDI permits multiple companies […]
What is Electronic Data Interchange (EDI)? Electronic Data Interchange (EDI) is the transfer of data from one computer system to another by standardized message formatting without the need for human intervention. The goal of EDI is to replace manual processes that involve the exchange of documents with a fully autonomous one. EDI permits multiple companies […]
Apr 24, 2024NewsroomMalware / Data Security A new ongoing malware campaign has been observed distributing three different stealers, such as CryptBot, LummaC2, and Rhadamanthys hosted on Content Delivery Network (CDN) cache domains since at least February 2024. Cisco Talos has attributed the activity with moderate confidence to a threat actor tracked as CoralRaider, a suspected […]
A dependency confusion vulnerability has been found within an archived Apache project. According to new data by Legit Security, who made the discovery, the finding underscores the importance of scrutinizing third-party projects and dependencies, particularly those archived and potentially neglected in terms of updates and security patches. The technical post, published today, suggests that despite […]
What is free cooling? Free cooling is an approach to lowering the air temperature in a building or data center by using naturally cool air or water instead of mechanical refrigeration. In practice, free cooling is not entirely free because pumps, fans, and other air and water-handling equipment is needed. That equipment also requires periodic […]