Apr 17, 2024NewsroomVulnerability / Web Application Firewall Cybersecurity researchers have discovered a new campaign that’s exploiting a recently disclosed security flaw in Fortinet FortiClient EMS devices to deliver ScreenConnect and Metasploit Powerfun payloads. The activity entails the exploitation of CVE-2023-48788 (CVSS score: 9.3), a critical SQL injection flaw that could permit an unauthenticated attacker to […]
Apr 18, 2024NewsroomMalvertising / Endpoint Security A new Google malvertising campaign is leveraging a cluster of domains mimicking a legitimate IP scanner software to deliver a previously unknown backdoor dubbed MadMxShell. “The threat actor registered multiple look-alike domains using a typosquatting technique and leveraged Google Ads to push these domains to the top of search […]
According to many reports, this is part of a campaign targeted at current and former mobile carrier workers who could have access to the systems required to perform a SIM swap.
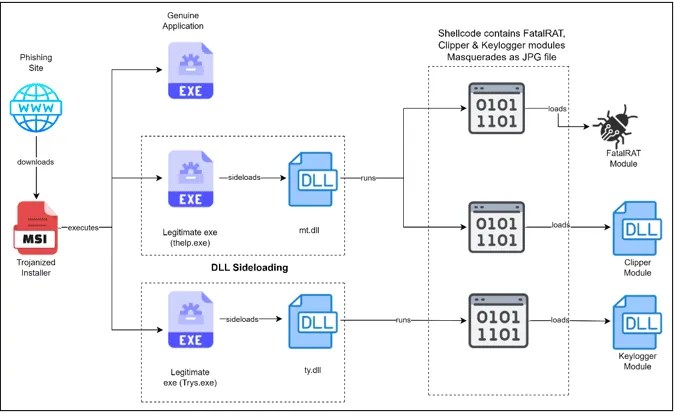
Researchers have discovered a sophisticated phishing campaign meticulously crafted to target cryptocurrency users. This elaborate scheme, equipped with the notorious FatalRAT along with supplementary malware like Clipper and Keylogger, was orchestrated by threat actors utilizing DLL side-loading techniques. Source: Infection Chain (Cyble) FatalRAT, renowned as a Remote Access Trojan, grants attackers control over victim systems, […]
While the mobile phishing campaign has yet to reach some U.S. regions, this can be explained by the fact that complaint information collected so far by IC3 indicates the scam may be moving from state to state.
An ongoing malvertising campaign is targeting IT administrators looking to download system utilities such as PuTTY (a free SSH and Telnet client) and FileZilla (a free cross-platform FTP application). “We have reported this campaign to Google but no action has been taken yet,” , Malwarebytes researcher Jérôme Segura shared. The campaign Malicious ads served via […]
In a recent attack campaign, cybercriminals were discovered cleverly manipulating GitHub’s search functionality, and using meticulously crafted repositories to distribute malware. Key Points GitHub search manipulation: Attackers create malicious repositories with popular names and topics, using techniques like automated updates and fake stars to boost search rankings and deceive users. Malicious code is often hidden […]
ARC Labs recently analyzed a phishing email used in a credential harvesting campaign that leveraged a lure notifying the target they received a voice message and needed to visit a link to access it. Analysis of the payload revealed heavily obfuscated HTML data which executed JavaScript code embedded within an SVG image when the page […]
Apr 10, 2024NewsroomMobile Security / Spyware An active Android malware campaign dubbed eXotic Visit has been primarily targeting users in South Asia, particularly those in India and Pakistan, with malware distributed via dedicated websites and Google Play Store. Slovak cybersecurity firm said the activity, ongoing since November 2021, is not linked to any known threat […]