Cybersecurity
Category Added in a WPeMatico Campaign
The initial infection vector is a Word document that downloads and executes a 64-bit Rust-compiled binary. This binary then downloads an encoded shellcode containing the AgentTesla payload.
Apr 28, 2024NewsroomCredential Stuffing / Data Breach Identity and access management (IAM) services provider Okta has warned of a spike in the “frequency and scale” of credential stuffing attacks aimed at online services. These unprecedented attacks, observed over the last month, are said to be facilitated by “the broad availability of residential proxy services, lists […]
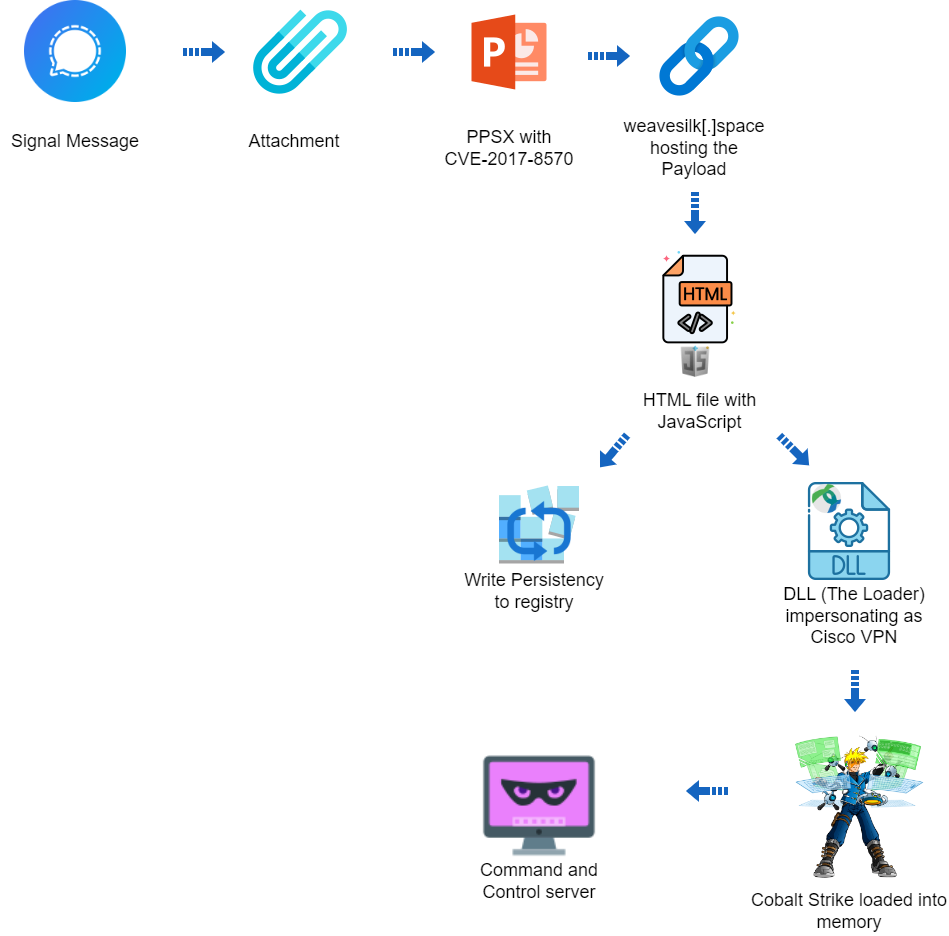
Apr 27, 2024NewsroomCyber Attack / Malware Cybersecurity researchers have discovered a targeted operation against Ukraine that has been found leveraging a nearly seven-year-old flaw in Microsoft Office to deliver Cobalt Strike on compromised systems. The attack chain, which took place at the end of 2023 according to Deep Instinct, employs a PowerPoint slideshow file (“signal-2023-12-20-160512.ppsx”) […]
Nearly five months after security researchers warned of the Cactus ransomware group leveraging a set of three vulnerabilities in Qlik Sense data analytics and business intelligence (BI) platform, many organizations remain dangerously vulnerable to the threat. Qlik disclosed the vulnerabilities in August and September. The company’s August disclosure involved two bugs in multiple versions of […]
Cybercriminals are taking advantage of people’s fears about online dating by getting them to download fake “verification” apps that allow them to steal information and money. The FBI published a warning on Friday about the scam, noting that it was akin to an offshoot of romance scams and pig butchering schemes that have proliferated in […]
Apr 27, 2024NewsroomMalware / Software Security An ongoing social engineering campaign is targeting software developers with bogus npm packages under the guise of a job interview to trick them into downloading a Python backdoor. Cybersecurity firm Securonix is tracking the activity under the name DEV#POPPER, linking it to North Korean threat actors. “During these fraudulent […]
Executive Summary The Deep Instinct Threat Lab discovered a suspected targeted operation against Ukraine The operation is using CVE-2017-8570 as the initial vector The operation could not be attributed to any known threat actor The operation used a custom loader for Cobalt Strike Beacon Deep Instinct is detecting all stages of the attack Campaign Overview […]
Apr 26, 2024NewsroomSupply Chain Attack / Software Security Several security vulnerabilities disclosed in Brocade SANnav storage area network (SAN) management application could be exploited to compromise susceptible appliances. The 18 flaws impact all versions up to and including 2.3.0, according to independent security researcher Pierre Barre, who discovered and reported them. The issues range from […]
The malware is delivered through a fake Google Chrome update that is shown while using the web browser. Brokewell is under active development and features a mix of extensive device takeover and remote control capabilities.