Cybersecurity
Category Added in a WPeMatico Campaign
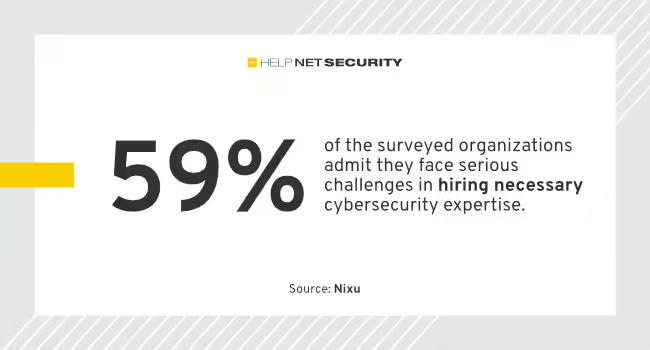
Over 80% of northern European organizations emphasize that the need to ensure business resilience is the top driver for their cybersecurity investments, according to Nixu. The report reveals both encouraging progress and increasing concerns. Alarmingly, 50% of organizations reach only a poor or deficient level in cybersecurity. “The prominence of business resilience as a driver […]
The attack involves the deployment of a trojanized version of the UTetris application, which acts as a loader for malware and facilitates the spread of the attack to potentially air-gapped systems.
Dive Brief: Worldwide IT spending is expected to surge to $5.1 trillion in 2024, growing 8% year over year, analyst firm Gartner projected in a Wednesday report. This marks the first time IT spending is expected to surpass $5 trillion. AI is already having an influence and is set to impact one area of IT […]
It is speculated that the threat actors behind the attacks may be deploying an update to hide their presence, or a grey-hat hacker could be rebooting the devices to clear the implant.
In many cases, senior executives/line-of-business leaders are minimally engaged in their company’s cyber preparedness initiatives — only 33% of CEOs or managing directors and 21% of other senior leaders are heavily involved, according to Commvault. According to the research, 52% of senior leaders have no involvement in their company’s cyber cases. In addition to a […]
Researchers have discovered possible signs of cooperation between the Palestinian militant organization Hamas and one of the longest-running groups of Arabic-speaking hackers. According to a report published Thursday by researchers at Recorded Future, Hamas has allegedly turned to operators outside Gaza and “third parties” to keep a news website linked to its military wing, Al-Qassam […]
A “key target” allegedly involved with the Ragnar Locker ransomware group was arrested in Paris on Monday, according to officials at Europol. The announcement, made Friday, is the first official word from law enforcement after the gang’s leak site was replaced with a banner featuring the insignias of several agencies on Thursday. Europol said law […]
Venture capital investments in cybersecurity firms keeps shrinking with less capital raised and fewer deals compared to the year prior, according to Crunchbase data released Thursday. Cybersecurity startups raised almost $1.9 billion during the third quarter, marking a 30% drop from the $2.7 billion raised in the year-ago period. The 153 deals in the quarter […]
Enlarge Getty Images Identity and authentication management provider Okta said hackers managed to view private customer information after gaining access to credentials to its customer support management system. “The threat actor was able to view files uploaded by certain Okta customers as part of recent support cases,” Okta Chief Security Officer David Bradbury said Friday. […]