Cybersecurity
Category Added in a WPeMatico Campaign
The vulnerability, tracked as CVE-2023-6553, can be exploited by unauthenticated attackers without user interaction. Although a patch has been released, almost 50,000 WordPress websites still remain vulnerable to this critical security flaw.
Cybercriminals still prefer targeting open remote access products, or like to leverage legitimate remote access tools to hide their malicious actions, according to WatchGuard. “Threat actors continue using different tools and methods in their attack campaigns, making it critical for organizations to keep abreast of the latest tactics to fortify their security strategy,” said Corey […]
A ransomware attack in April on cold storage giant Americold affected nearly 130,000 people, the company has announced. In a breach report to regulators in Maine on Friday, Atlanta-based Americold confirmed that hackers had breached its systems on April 26 and accessed the information of current and former Americold employees as well as their dependents. […]
Dec 12, 2023The Hacker NewsCybersecurity / GenAI Security 2023 has seen its fair share of cyber attacks, however there’s one attack vector that proves to be more prominent than others – non-human access. With 11 high-profile attacks in 13 months and an ever-growing ungoverned attack surface, non-human identities are the new perimeter, and 2023 is […]
Killmilk, the leader of the pro-Russia hacktivist group Killnet, announced his “retirement” this week and appointed a new head for the gang. “From now on, I am no longer a part of Killnet! I’m retiring…,” he said in a Telegram post. Russia’s war in Ukraine “has taken a toll on my nerves and strength. I […]
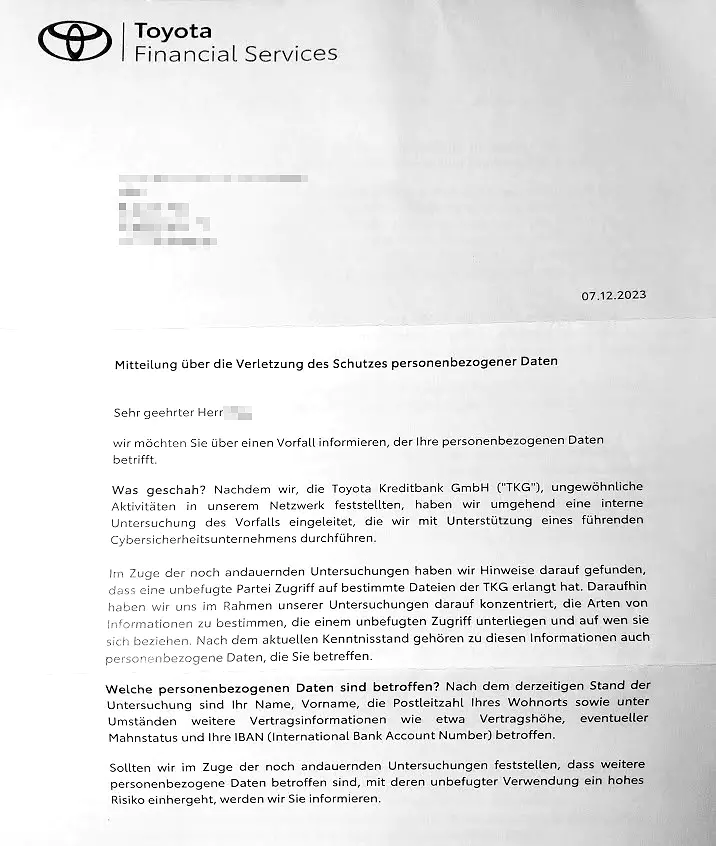
Toyota Financial Services discloses a data breach Pierluigi Paganini December 11, 2023 Toyota Financial Services (TFS) disclosed a data breach, threat actors had access to sensitive personal and financial data. Toyota Financial Services (TFS) is warning customers it has suffered a data breach that exposed sensitive personal and financial data. “Due to an attack on […]
Police in Lancashire in North West England have managed to return around £8 million ($10 million) in bitcoin to a man whose cryptocurrency was stolen back in 2017. It follows four people being sentenced earlier this year for their part in a £20 million ($25 million) hack after they discovered a glitch in how the […]
A group of hackers targeted a television service in the United Arab Emirates over the weekend, replacing the original broadcast with graphic footage from the war between Israel and Hamas. Several UAE citizens affected by the hack told the Dubai-based newspaper Khaleej Times that television programs aired on European live channels, including BBC News, were […]
Dec 12, 2023NewsroomCryptocurrency / Cyber Attack A phishing campaign has been observed delivering an information stealer malware called MrAnon Stealer to unsuspecting victims via seemingly benign booking-themed PDF lures. “This malware is a Python-based information stealer compressed with cx-Freeze to evade detection,” Fortinet FortiGuard Labs researcher Cara Lin said. “MrAnon Stealer steals its victims’ credentials, […]