Cybersecurity
Category Added in a WPeMatico Campaign
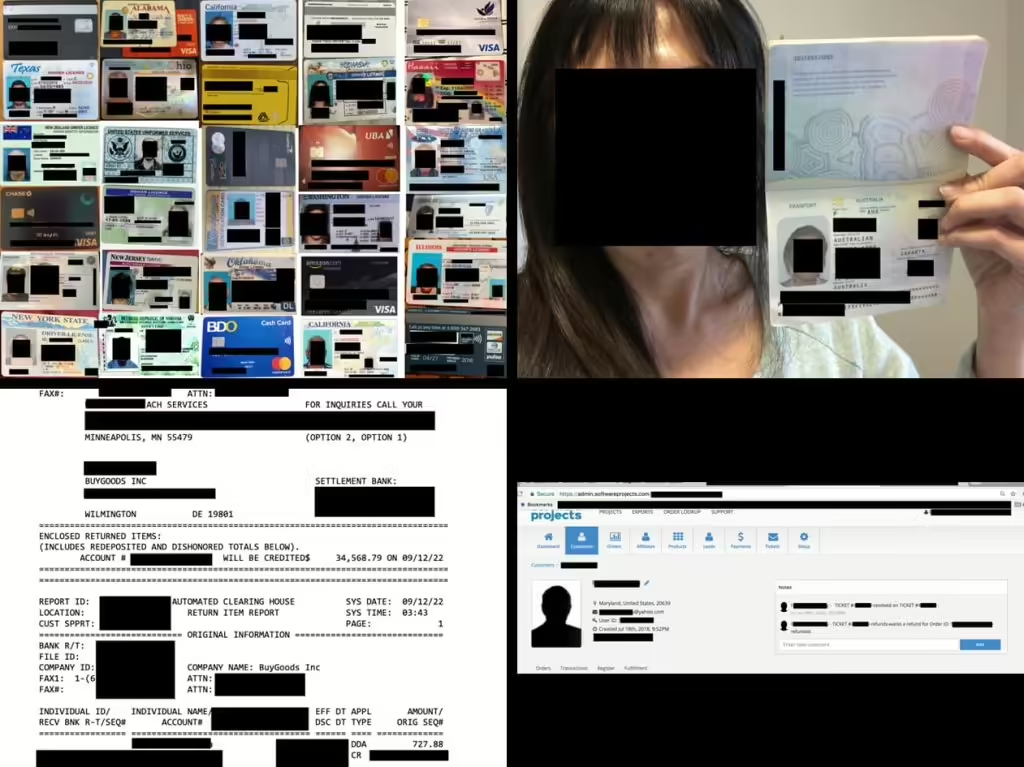
The staggering 198.3 gigabytes of misconfigured database contained more than 260,000 records including customer selfies with unredacted credit cards. Cybersecurity researcher Jeremiah Fowler recently uncovered a misconfigured cloud database that had left a wealth of sensitive data exposed. The affected database contained records attributed to customers of BuyGoods.com, alternatively recognized in the industry as Softwareproject. […]
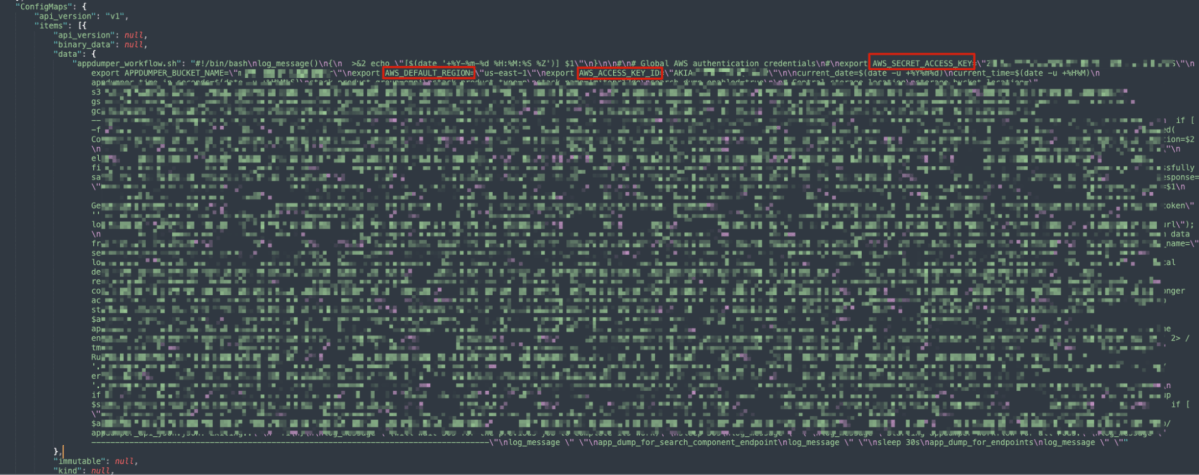
Following our discovery of a critical loophole in Google Kubernetes Engine (GKE) dubbed Sys:All, we decided to conduct research into the real-world impacts of this issue. Our initial probe already revealed over a thousand vulnerable GKE clusters due to admins configuring RBAC bindings making the system:authenticated group overprivileged, which could potentially allow any Google account […]
The company has discovered a limited number of individuals whose personal information may have been impacted during the breach and is working with a third-party forensics firm to assess the extent of the attack’s impact on its operations and systems.
KB5034204 also fixes an issue caused by a deadlock that prevents search from working on the Start menu for some users and addresses a bug affecting the OpenType font driver, affecting how text renders for third-party applications.
ReversingLabs researchers have discovered two malicious packages on the npm open source package manager that leverages GitHub to store stolen Base64-encrypted SSH keys lifted from developer systems that installed the malicious npm packages.
Jan 24, 2024NewsroomCloud Security / Kubernetes Cybersecurity researchers have discovered a loophole impacting Google Kubernetes Engine (GKE) that could be potentially exploited by threat actors with a Google account to take control of a Kubernetes cluster. The critical shortcoming has been codenamed Sys:All by cloud security firm Orca. As many as 250,000 active GKE clusters […]
Ransomware In this blog, we detail our investigation of the Kasseika ransomware and the indicators we found suggesting that the actors behind it have acquired access to the source code of the notorious BlackMatter ransomware. By: Emmanuel Panopio, Christian Jason Geollegue, Julius Keith Estrellado, Christian Alpuerto, Shawn Austin Santos, Emmanuel Roll, Rhio Manaog, Gerald Fernandez, […]
Jan 24, 2024The Hacker NewsSaaS Security / Endpoint Security In today’s highly distributed workplace, every employee has the ability to act as their own CIO, adopting new cloud and SaaS technologies whenever and wherever they need. While this has been a critical boon to productivity and innovation in the digital enterprise, it has upended traditional […]
The ransomware group known as Kasseika has become the latest to leverage the Bring Your Own Vulnerable Driver (BYOVD) attack to disarm security-related processes on compromised Windows hosts, joining the likes of other groups like Akira, AvosLocker, BlackByte, and RobbinHood. The tactic allows “threat actors to terminate antivirus processes and services for the deployment of […]