Progress Software released fixes for eight vulnerabilities in WS_FTP, including one with a maximum severity score, but evidence of exploitation was discovered shortly after.
Sep 30, 2023THNEmail Security / Hacking News Multiple security vulnerabilities have been disclosed in the Exim mail transfer agent that, if successfully exploited, could result in information disclosure and remote code execution. The list of flaws, which were reported anonymously way back in June 2022, is as follows – CVE-2023-42114 (CVSS score: 3.7) – Exim […]
Researchers who discovered two critical vulnerabilities in Microsoft SharePoint Server have released details of an exploit they developed that chains the two vulnerabilities together to enable remote code execution on affected servers. Separately, another security researcher this week posted proof-of-concept code on GitHub for one of the SharePoint vulnerabilities that shows how an attacker could […]
The Known Exploited Vulnerabilities (KEV) Catalog maintained by the US cybersecurity agency CISA has led to significant improvements in federal agencies’ patching efforts, with more than 1,000 vulnerabilities now included in the list. Launched in November 2021, the KEV Catalog lists flaws that CISA has proof are being exploited in malicious attacks, and is accompanied […]
Apple released emergency security updates to patch three new zero-day vulnerabilities exploited in attacks targeting iPhone and Mac users, for a total of 16 zero-days fixed this year.
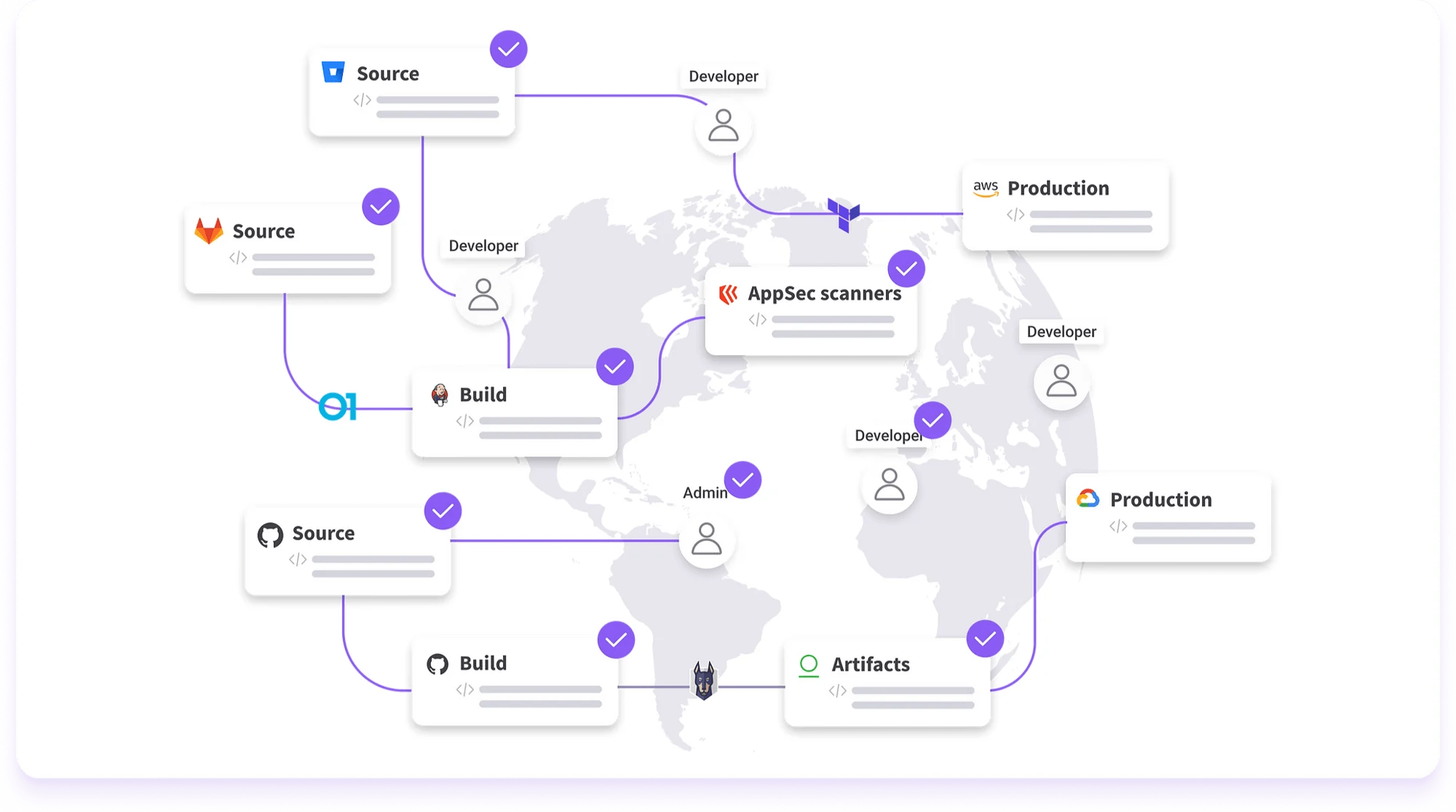
Legit Security, a cybersecurity company developing a platform to identify app vulnerabilities from code, has raised $40 million in a Series B funding round led by CRV with participation from Cyberstarts, Bessemer Venture Partners and TCV. Co-founder and CEO Roni Fuchs says that the funds, which bring Legit’s total raised to $77 million, will be […]
Atlassian this week announced patches for four high-severity vulnerabilities impacting its Jira, Confluence, Bitbucket, and Bamboo products. Tracked as CVE-2023-22513 (CVSS score of 8.5), the most severe of these issues is described as a remote code execution (RCE) bug in Bitbucket that could impact confidentiality, integrity, and availability. An authenticated attacker can exploit the flaw […]
Two vulnerabilities discovered earlier this year in Atos Unify products could allow malicious actors to cause disruption and even backdoor the targeted system. The flaws were found in the unified communications and collaboration solution by researchers at SEC Consult, an Austria-based cybersecurity consulting firm that is part of the Atos Group’s Eviden business. The vulnerabilities […]
Three high-severity Kubernetes vulnerabilities (CVE-2023-3676, CVE-2023-3893, CVE-2023-3955) could allow attackers to execute code remotely and gain control over all Windows nodes in the Kubernetes cluster. About the vulnerabilities CVE-2023-3676, discovered by Akamai researcher Tomer Peled, is a command injection vulnerability that can be exploited by applying a malicious YAML file on the cluster. “The Kubernetes […]