Shared bank accounts are convenient, but they can hinder your financial autonomy.
Cold-brew makers aren’t like coffee machines. They don’t push steam through a tight puck of coffee grounds or heat water to drip over them. Most cold-brew makers are simple devices, and that’s because cold-brewing coffee is a deceptively simple process. We don’t actually need a cold-brew maker to do much. We don’t want it to […]
The smart home doesn’t always feel smart. I test a lot of devices for a living, and they take a lot of babysitting and steps to do everything you want. Whether you’re setting up skills on an Alexa speaker or getting your smart lights on the right schedule–shout-out to Daylight Savings for ruining my existing […]
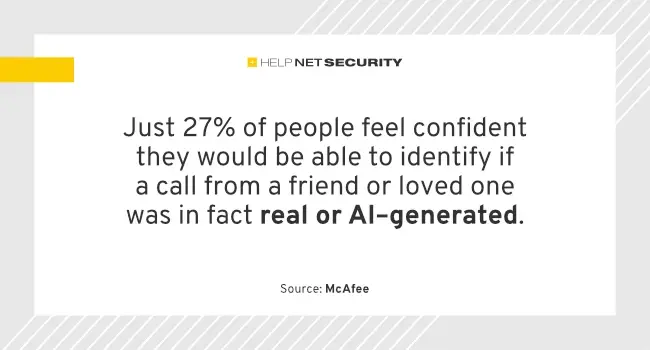
23% of Americans said they recently came across a political deepfake they later discovered to be fake, according to McAfee. The actual number of people exposed to political and other deepfakes is expected to be much higher given many Americans are not able to decipher what is real versus fake, thanks to the sophistication of […]
Apr 23, 2024NewsroomCounterintelligence / National Security German authorities said they have issued arrest warrants against three citizens on suspicion of spying for China. The full names of the defendants were not disclosed by the Office of the Federal Prosecutor (aka Generalbundesanwalt), but it includes Herwig F., Ina F., and Thomas R. “The suspects are strongly […]
An operator of the HelloKitty ransomware operation announced they changed the name to ‘HelloGookie,’ releasing passwords for previously leaked CD Projekt source code, Cisco network information, and decryption keys from old attacks.
Sandboxes are synonymous with dynamic malware analysis. They help to execute malicious files in a safe virtual environment and observe their behavior. However, they also offer plenty of value in terms of static analysis. See these five scenarios where a sandbox can prove to be a useful tool in your investigations. Detecting Threats in PDFs […]
Apr 10, 2024NewsroomHardware Security / Linux Cybersecurity researchers have disclosed what they say is the “first native Spectre v2 exploit” against the Linux kernel on Intel systems that could be exploited to read sensitive data from the memory. The exploit, called Native Branch History Injection (BHI), can be used to leak arbitrary kernel memory at […]
Data centers use AI tools to manage the facilities and the workloads they handle. AI can help data center admins with various tasks, including power control, energy consumption monitoring, maintenance updates and network security. AI is an ever-changing business discipline for today’s data centers. Admins must learn everything from how to deploy the latest AI […]