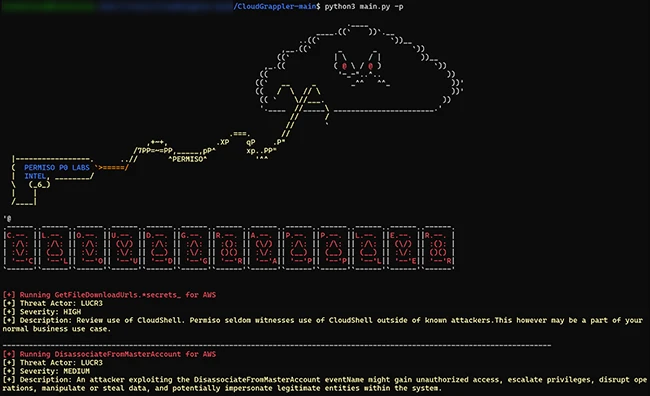
CloudGrappler is an open-source tool designed to assist security teams in identifying threat actors within their AWS and Azure environments. The tool, built on the foundation of Cado Security’s cloudgrep project, offers enhanced detection capabilities based on the tactics, techniques, and procedures (TTPs) of modern cloud threat actors like LUCR-3 (Scattered Spider). CloudGrappler queries for […]
Security teams are hiding an embarrassing secret from the outside world: despite their position at the vanguard of technology, security risks and threats, their actual war plans are managed on spreadsheets. This is a far cry from the dark rooms, multi-screens, and falling code most people imagine, and it’s also a universe away from what […]
97% of office workers across the UK and US trust their cybersecurity team’s ability to prevent or minimize damage from cyberattacks, according to CybSafe. The study examining attitudes towards cybersecurity teams within organizations has uncovered that despite minor issues around communication and processes, there are high levels of trust and appreciation amongst employees. It indicates […]
The attackers exploit default settings in Teams to send over 1,000 malicious chat invites. Once the attachment is downloaded, the malware connects to a command-and-control server.
A new user is signing up for a SaaS application. On the one hand, UX teams want that user to get into the app as quickly as possible. On the other hand, security teams want the user to strongly validate their identity and configure settings properly before they enter sensitive information. Two worlds collide in […]
Russian producer teams up with Japanese vocalist Eiko Hara for maximum bliss St Petersburg’s Mikhail Khvasko AKA A Vision of Panorama is incredibly good at making warming, summer-ready Balearic beats – which is why need him more than ever right now. His latest EP for Cala Tarida Musica sees him team up with Japanese singer […]
What do basketball teams, government agencies, and car manufacturers have in common? Each one has been breached, having confidential, proprietary, or private information stolen and exposed by insiders. In each case, the motivations and methods varied, but the risk remained the same: insiders have access to too much data with too few controls. Insider threats […]
Nov 02, 2023NewsroomVulnerability Assessment The Forum of Incident Response and Security Teams (FIRST) has officially announced CVSS v4.0, the next generation of the Common Vulnerability Scoring System standard, more than eight years after the release of CVSS v3.0 in June 2015. “This latest version of CVSS 4.0 seeks to provide the highest fidelity of vulnerability […]
A spearphishing campaign targeting management teams associated with an Azerbaijanian company exploits the conflict between Azerbaijan and Armenia, using malware disguised as an infected memo to gather basic computer information from its targets.
- 1
- 2