Technical Analysis In the following sections, we dive into the technical details surrounding Zloader’s new updates to their anti-analysis techniques, embedded configuration, DGA, and network encryption. Anti-analysis techniques Zloader uses a combination of API import hashing, junk code, a filename check, and string obfuscation. The following sections analyze each technique. Imports and API resolution The […]
Enlarge Tero Vesalainen Researchers on Wednesday presented intriguing new findings surrounding an attack that over four years backdoored dozens if not thousands of iPhones, many of which belonged to employees of Moscow-based security firm Kaspersky. Chief among the discoveries: the unknown attackers were able to achieve an unprecedented level of access by exploiting a vulnerability […]
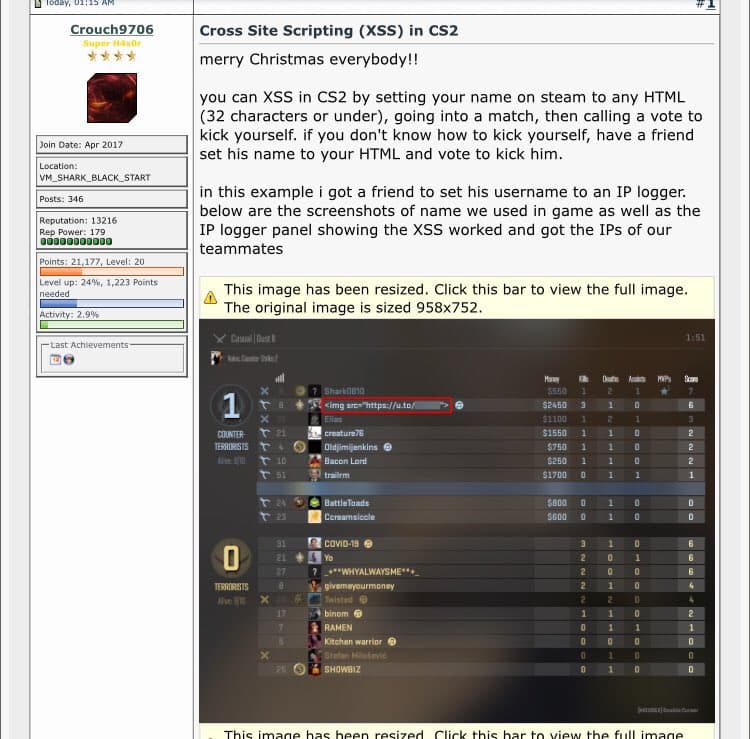
Valve, the developer of Counter Strike 2, is expected to address the rumours surrounding the new CS2 exploit. Meanwhile, be cautious and watch out for suspicious links from unknown senders. A recently uncovered CS2 exploit (apparently an XSS vulnerability) has raised concerns within the gaming community, posing a potential threat to player security. This exploit […]