Email attacks relying on QR codes surged in the last quarter, with attackers specifically targeting corporate executives and managers, reinforcing recommendations that companies place additional digital protections around their business leadership. Making matters worse, phishing emails using QR codes (aka “quishing”) can often get by spam filters, with attacks targeting users of Microsoft 365 and […]
What is the GNU project? The GNU project is a mass collaborative initiative for the development of free software, specifically a free operating system called GNU. Of course, “free”, in a software context, does not necessarily mean “free of cost”. Rather, free refers to the freedom that users have to use, study, share and improve […]
A critical vulnerability has been identified in the AI Engine plugin for WordPress, specifically affecting its free version with over 50,000 active installations. The plugin is widely recognized for its diverse AI-related functionalities, allowing users to create chatbots, manage content and utilize various AI tools such as translation, SEO and more. According to an advisory […]
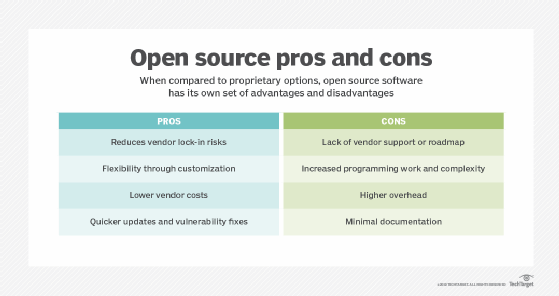
AuthLogParser is an open-source tool tailored for digital forensics and incident response, specifically crafted to analyze Linux authentication logs (auth.log). The tool examines the auth.log file, extracting crucial details like SSH logins, user creations, event names, IP addresses, among others. It produces a concise summary that offers a clear overview of the activities documented in […]
Barracuda Networks recently encountered a challenge as it uncovered two zero-day vulnerabilities, specifically CVE-2023-7102 and CVE-2023-7101. These Barracuda vulnerabilities were intricately linked to the Spreadsheet::ParseExcel library, revealing an Arbitrary Code Execution (ACE) flaw in the third-party library. Exploited by the China Nexus actor UNC4841, these security flaws posed a serious threat by targeting Barracuda Email […]
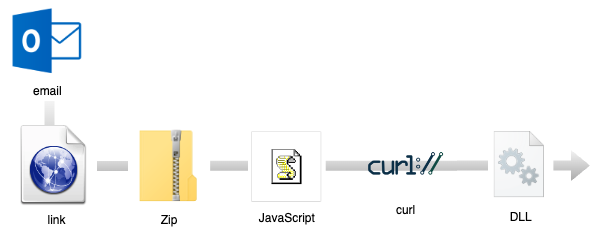
During this past year, we have seen an increase in the use of malicious ads (malvertising) and specifically those via search engines, to drop malware targeting businesses. In fact, browser-based attacks overall have been a lot more common if we include social engineering campaigns. Criminals have found success in acquiring new victims thanks to search […]