How It Works The sequence begins with threat actors creating a fake site on a web hosting service, which remains undetected by the hosting service itself. When a user searches for relevant information and clicks on a link from the search results, they unknowingly access the malicious site. Interestingly, if the user directly enters the […]
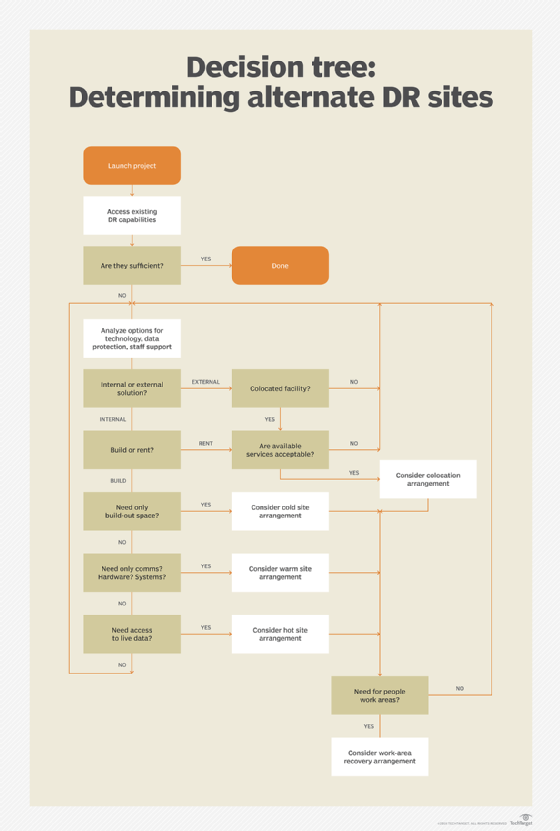
What is a disaster recovery (DR) site? A disaster recovery (DR) site is a facility an organization can use to recover and restore its technology infrastructure and operations when its primary data center becomes unavailable. The decision about what kind of DR site an organization needs and its location requires careful planning and a balance […]
Browser fingerprinting is one of many tactics phishing site authors use to evade security checks and lengthen the lifespan of malicious campaigns. While browser fingerprinting has been used by legitimate organizations to uniquely identify web browsers for nearly 15 years, it is now also commonly exploited by cybercriminals: a recent study shows one in four […]
An international group of law enforcement agencies has seized the dark web leak site of the notorious ransomware gang known as ALPHV, or BlackCat. “The Federal Bureau of Investigation seized this site as part of a coordinated law enforcement action taken against ALPHV Blackcat Ransomware,” a message on the gang’s dark web leak site now […]
The UK’s most hazardous nuclear site, Sellafield, has been hacked into by cyber groups closely linked to Russia and China, the Guardian can reveal. The astonishing disclosure and its potential effects have been consistently covered up by senior staff at the vast nuclear waste and decommissioning site, the investigation has found. The Guardian has discovered […]
The BlackCat ransomware gang added Henry Schein to its dark web leak site, saying it breached the company’s network and allegedly stole 35 terabytes of sensitive data. It re-encrypted the company’s devices after negotiations faltered.
The Daixin Team group added NTMWD to the list of victims on its Tor leak site. The gang claims to have stolen a huge amount of sensitive data from the company and threatens to publish it.
When users click on the ad, they are redirected to a fake Windows news site, where they are prompted to download a digitally signed CPU-Z installer. This installer contains a malicious PowerShell script known as the ‘FakeBat’ malware loader.
More often than not, its our solemn duty on this site to keep you informed about the nature and tactics of dangerous, cunnning, and persistent cybercriminals. This is not one of those days. In fact, this is the oppposite of one of those days. This is about a passable spam email sent by a spammer […]
- 1
- 2