Cybersecurity researchers from Bitdefender discovered critical vulnerabilities in LG TVs running webOS versions 4 through 7. These vulnerabilities could allow attackers to gain complete control over the TV, steal data, or install malware. The vulnerabilities were identified by Bitdefender as part of their research into the security of popular IoT devices. They found that attackers […]
Apr 09, 2024NewsroomVulnerability / IoT Security Multiple security vulnerabilities have been disclosed in LG webOS running on its smart televisions that could be exploited to bypass authorization and gain root access on the devices. The findings come from Romanian cybersecurity firm Bitdefender, which discovered and reported the flaws in November 2023. The issues were fixed […]
Mar 06, 2024NewsroomServer Security / Cryptocurrency Threat actors are targeting misconfigured and vulnerable servers running Apache Hadoop YARN, Docker, Atlassian Confluence, and Redis services as part of an emerging malware campaign designed to deliver a cryptocurrency miner and spawn a reverse shell for persistent remote access. “The attackers leverage these tools to issue exploit code, […]
Two Chinese nationals have been found guilty of running a sophisticated fraud scheme in which they attempted to con Apple out of millions of dollars, by sending it thousands of fake iPhones. Haotian Sun (aka Hao Sun, Jack Sun) of Baltimore, Maryland, and Pengfei Xue, 33, of Germantown, Maryland, were convicted of mail fraud and conspiracy […]
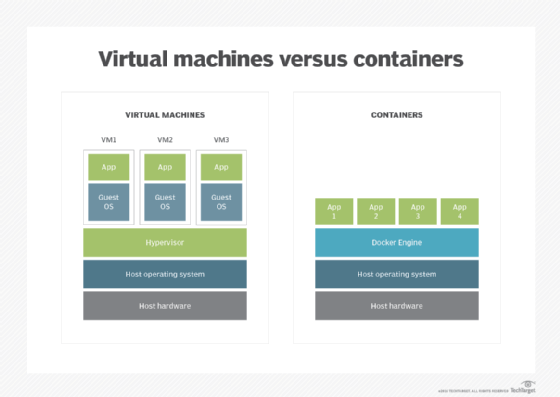
What is a hypervisor? A hypervisor is software that facilitates running multiple virtual machines (VMs) with their own operating systems on a single computer host’s hardware. The host machine and its physical hardware resources independently operate one or more VMs as guest operating systems. Multiple guest VMs share the system’s physical compute resources, including processor […]
(TNS) — Though Tri-City Medical Center got its operations back up and running 17 days ago, ransomware extortion efforts appear to be ongoing against the Oceanside hospital. Earlier this week, a cybersecurity expert noted in a message on X, formerly called Twitter, that “INC RANSOM”, a well known group of cyber extortionists, announced its possession […]
A recent attack levied against servers running out-of-date Adobe software sheds some light on how threat actors are currently trying to exploit systems and deploy ransomware. In this recent attack, which took place in September and early October, the threat actors hoped to gain access to Windows servers and, subsequently, deploy ransomware payloads. While the […]
Research by: Jiri Vinopal Highlights Check Point Research (CPR) introduces a new method for running hidden implanted code in ReadyToRun (R2R) compiled .NET binaries, R2R stomping. We explain the implementation of R2R stomping with a focus on its internals. The resulting problems of the R2R stomping technique will affect the work of the reverse engineers […]
Clorox said all of its manufacturing facilities were back up and running following an August cyberattack that led to weeks of disruption and product shortages, according to a Friday update. The Oakland, California-based maker of Pine-Sol and household bleach, said it resumed automated order processing on Sept. 25 and was ramping up the pace of production […]