In a result of its research investigation efforts, Security Explorations, a research lab of AG Security Research company, conducted security analysis of Microsoft Warbird and Protected Media Path technologies. This section of our website presents initial information regarding the project. Microsoft Warbird and Protected Media Path description Microsoft Protected Media Path (PMP) is a set […]
Critical Infrastructure Security Hacks on Unregulated Dams Can Result in Mass Casualties, Experts and Lawmakers Warn Chris Riotta (@chrisriotta) • April 18, 2024 Dams need better cybersecurity, warn experts. (Image: Shutterstock) Could a hacker seize control of America’s dams, unleashing floods and chaos across vulnerable communities? Cybersecurity analysts and leading lawmakers warn it’s […]
Enlarge Getty Images OpenAI officials say that the ChatGPT histories a user reported result from his ChatGPT account being compromised. The unauthorized logins came from Sri Lanka, an Open AI representative said. The user said he logs into his account from Brooklyn, New York. “From what we discovered, we consider it an account take over […]
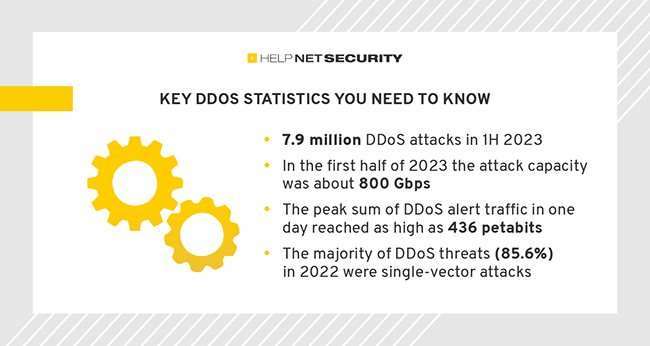
The impact of DDoS attacks extends far beyond mere inconvenience, as they can result in financial losses, compromised data, and erosion of customer trust. Understanding the nature and consequences of DDoS activity is essential for organizations and individuals alike as they strive to protect their online presence and ensure the uninterrupted flow of critical services. […]
As a result of the investigation, disciplinary action has been taken against 15 Air National Guard leaders, including the removal of commanders, and the USAF has implemented reforms to strengthen classified data access standards.
Most, if not all malvertising incidents result from a threat actor either injecting code within an existing ad, or intentionally creating one. Today, we look at a different scenario where, as strange as that may sound, malvertising was entirely accidental. The reason this happened was due to the combination of two separate factors: a compromised website […]
The hospitals’ IT provider, TransForm, is investigating the incident and determining if patient data was compromised. As a result of the outage, online services such as patient records and email have been affected.