akinbostanci/Getty Images Modern professionals have busy workloads and juggling all these demands is tough, especially when unexpected challenges appear on the horizon. Research suggests more than half (57%) of IT managers have to manage more incidents than they can handle. Also: 5 ways to manage your time more effectively at work If you don’t manage […]
The concept of Everywhere Work is now much broader, encompassing where, when, and how professionals get their work done — and flexibility has become a key workplace priority, according to Ivanti. Ivanti surveyed over 7,700 executive leaders, IT and cybersecurity professionals , and office workers to explore the profound challenges and opportunities employers face when […]
The Misconfiguration Manager repository provides a comprehensive resource for both offensive professionals and defenders to understand and manage the attack path related to Microsoft Configuration Manager (MCM), formerly known as SCCM.
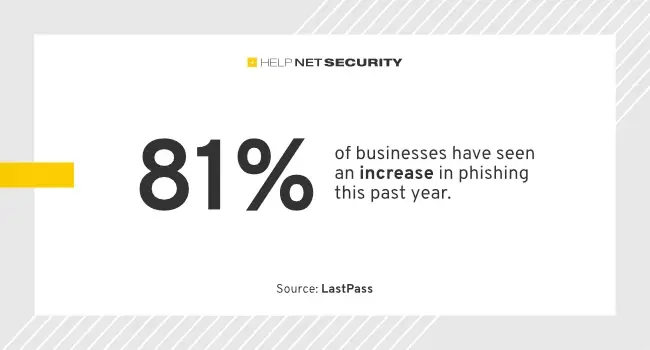
More than 95% of responding IT and security professionals believe social engineering attacks have become more sophisticated in the last year, according to LastPass. Recent AI advancements, particularly generative AI, have empowered cybercriminals to coordinate social engineering assaults with unprecedented precision and customization. Phishing and other social engineering attacks manipulate people into sharing information they […]
Processing alerts quickly and efficiently is the cornerstone of a Security Operations Center (SOC) professional’s role. Threat intelligence platforms can significantly enhance their ability to do so. Let’s find out what these platforms are and how they can empower analysts. The Challenge: Alert Overload The modern SOC faces a relentless barrage of security alerts generated […]
Machine learning and artificial intelligence are popular buzzwords for today’s IT professionals, but in the case of your organization’s data centers, they hold real promise. ML software actively predicts situations faster than you or your team might notice them and maybe even solves them quicker. These systems are a logical extension of today’s hybrid data […]
82% of cybersecurity professionals have been working on implementing zero trust last year, and 16% should be on it by the end of this year. The challenges of zero trust implementation You’ve probably heard it before: zero trust is not a single product, but a security strategy that follows the principle of “never trust, always […]
Email security remained top of mind for cybersecurity professionals in 2023 as over nine in ten (94%) cyber decision-makers had to deal with a phishing attack, according to email security provider Egress. This is up 2% from the previous year, Egress’ Email Security Risk Report 2024 found. The top three phishing techniques used throughout 2023 […]
IT professionals have developed a sophisticated understanding of the enterprise attack surface – what it is, how to quantify it and how to manage it. The process is simple: begin by thoroughly assessing the attack surface, encompassing the entire IT environment. Identify all potential entry and exit points where unauthorized access could occur. Strengthen these […]
- 1
- 2