Apr 10, 2024The Hacker NewsWebinar / Identity Security We all know passwords and firewalls are important, but what about the invisible threats lurking beneath the surface of your systems? Identity Threat Exposures (ITEs) are like secret tunnels for hackers – they make your security way more vulnerable than you think. Think of it like this: […]
Users of Cutout.Pro are advised to reset their passwords immediately and be cautious of targeted phishing scams due to the potential threat of threat actors brute-forcing the leaked password hashes.
The breach did not compromise payment details, and U-Haul has reset passwords for affected accounts, implemented additional security measures, and offered one-year identity theft protection service to affected customers.
Members are advised to be cautious of phishing attacks and to update their passwords as a precautionary measure, while the organization has taken steps to enhance cybersecurity in response to the incident.
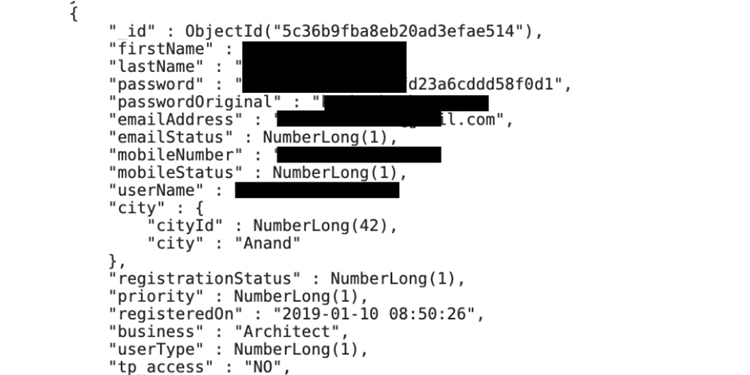
MyEstatePoint Property Search Android app leaks user passwords Pierluigi Paganini January 05, 2024 The MyEstatePoint Property Search app leaked data on nearly half a million of its users, exposing their names and plain-text passwords, the Cybernews research team has found. The all-in-one real estate app MyEstatePoint Property Search left a publicly accessible MongoDB server containing […]
LastPass, a popular password management solution, is now requiring customers to use complex master passwords with a minimum of 12 characters to enhance account security. Previously, users had the option to use weaker passwords.
Android barcode scanner app exposes user passwords Pierluigi Paganini December 08, 2023 An Android app with over 100k Google Play downloads and a 4.5-star average rating has let an open instance go unchecked, leaving sensitive user data up for grabs. The Cybernews team discovered the Android app Barcode to Sheet leaking sensitive user information and […]
Reportedly, the ransomware operators breached HSE by stealing passwords for HSE’s systems from an unprotected cloud storage instance. So far, the organization has not received a ransom demand but stated that it might be too early for this.
The vulnerability allows attackers to access files, execute code, and obtain passwords. The exploit takes advantage of an unauthenticated mass-assignment vulnerability and AS2 header parsing.
- 1
- 2