The Department of Defense provided new projections for how much money contractors and other organizations will have to spend to implement the Pentagon’s Cybersecurity Maturity Model Certification program. The updated estimates were included in a proposed rule for CMMC 2.0 that was published Tuesday in the Federal Register. The program would mandate that defense contractors […]
The Russia-based actor is targeting organizations and individuals in the UK and other geographical areas of interest. OVERVIEW The Russia-based actor Star Blizzard (formerly known as SEABORGIUM, also known as Callisto Group/TA446/COLDRIVER/TAG-53/BlueCharlie) continues to successfully use spear-phishing attacks against targeted organizations and individuals in the UK, and other geographical areas of interest, for information-gathering activity. […]
Other clean-up processes There are lots of other digital processes that some people like to apply to rips. You may hear people talking about subsonic rumble filters, “de-essing” filters, hiss reduction and more. These are all worth investigating, but my advice is to put more of your effort into having a properly set-up turntable and […]
Nov 27, 2023NewsroomArtificial Intelligence / Privacy The U.K. and U.S., along with international partners from 16 other countries, have released new guidelines for the development of secure artificial intelligence (AI) systems. “The approach prioritizes ownership of security outcomes for customers, embraces radical transparency and accountability, and establishes organizational structures where secure design is a top […]
Nov 21, 2023NewsroomRansomware-as-a-service The ransomware strain known as Play is now being offered to other threat actors “as a service,” new evidence unearthed by Adlumin has revealed. “The unusual lack of even small variations between attacks suggests that they are being carried out by affiliates who have purchased the ransomware-as-a-service (RaaS) and are following step-by-step […]
An Indian hack-for-hire group targeted the U.S., China, Myanmar, Pakistan, Kuwait, and other countries as part of a wide-ranging espionage, surveillance, and disruptive operation for over a decade. The Appin Software Security (aka Appin Security Group), according to an in-depth analysis from SentinelOne, began as an educational startup offering offensive security training programs, while carrying […]
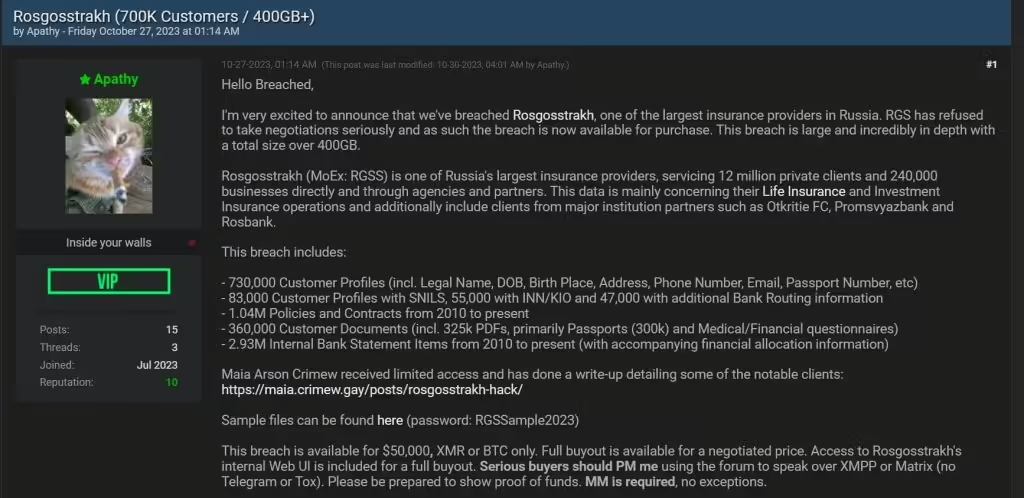
An analysis of the sample data shared by the hackers revealed, among other details, personal and insurance-related information belonging to three GRU agents. Since the beginning of the Russia-Ukraine conflict, both nations have experienced a series of non-stop large-scale cyberattacks targeting critical infrastructure, personal data of unsuspecting users, as well as sensitive military and banking […]
Researchers also targeted other devices such as smartphones, printers, smart speakers, and surveillance cameras, demonstrating the wide range of potential targets for hackers.
Vim was once the default editor with Linux. Now, with other text editors, like Nano, available to install, it may be difficult to decide what editor is best for you. The following tutorial and tips to using Vim with Linux will provide a better understanding on how to efficiently use the tool. Why use Vim? […]