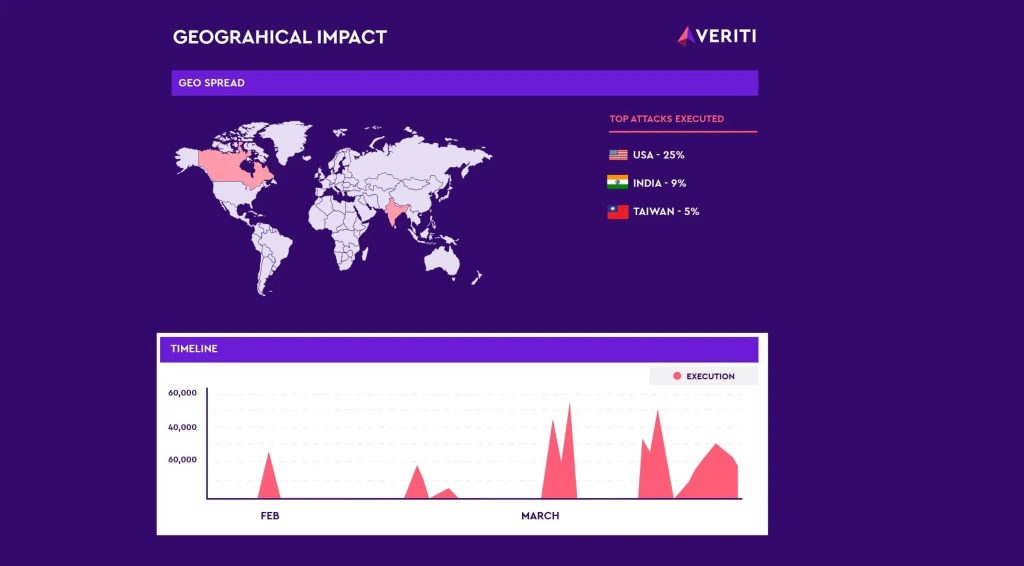
Veriti Research has discovered a surge in attacks from operators of the Androxgh0st malware family, uncovering over 600 servers compromised primarily in the U.S., India and Taiwan. According to Veriti’s blog post, the adversary behind Androxgh0st had their C2 server exposed, which could allow for a counterstrike by revealing the impacted targets. The researchers then […]
While the results of law enforcement action against ransomware-as-a-service operators Alphv/BlackCat and LockBit are yet to be fully realized, the August 2023 disruption of the Qakbot botnet has had one notable effect: ransomware affiliates have switched to vulnerability exploitation as the primary method of delivering the malware. The switch is obvious to Symantec’s Threat Hunter […]
Cybersecurity researchers have identified new infrastructure likely used by the operators of the commercial spyware known as Predator in at least 11 countries. By analyzing the domains likely used to deliver the spyware, analysts at Recorded Future’s Insikt Group were able to spot potential Predator customers in Angola, Armenia, Botswana, Egypt, Indonesia, Kazakhstan, Mongolia, Oman, […]
Feb 09, 2024NewsroomMalware / Dark Web The operators of Raspberry Robin are now using two new one-day exploits to achieve local privilege escalation, even as the malware continues to be refined and improved to make it stealthier than before. This means that “Raspberry Robin has access to an exploit seller or its authors develop the […]
Hundreds of network operators’ credentials found circulating in Dark Web Pierluigi Paganini January 30, 2024 Hundreds of compromised credentials of customers of RIPE, APNIC, AFRINIC, and LACNIC are available on the dark web, Resecurity warns. Resecurity conducted a thorough scan of the Dark Web and identified over 1,572 compromised customers of RIPE, Asia-Pacific Network Information […]
Jan 16, 2024NewsroomCryptocurrency / Cyber Threat The operators behind the now-defunct Inferno Drainer created more than 16,000 unique malicious domains over a span of one year between 2022 and 2023. The scheme “leveraged high-quality phishing pages to lure unsuspecting users into connecting their cryptocurrency wallets with the attackers’ infrastructure that spoofed Web3 protocols to trick […]
Affiliates associated with NoEscape claimed that the ransomware operators pulled an exit scam, stealing millions of dollars in ransom payments and shutting off the operation’s web panels and data leak sites.
Reportedly, the ransomware operators breached HSE by stealing passwords for HSE’s systems from an unprotected cloud storage instance. So far, the organization has not received a ransom demand but stated that it might be too early for this.
The motive behind these cloned sites is likely to generate traffic for gambling operators, as they can serve third-party ads that publishers may be reluctant to carry on their own sites.
- 1
- 2