CERT-UA reports that in March 2024, APT44 conducted operations to disrupt information and communication systems at energy, water, and heating suppliers in 10 regions of Ukraine.
What is IOPS (input/output operations per second)? IOPS (input/output operations per second) is the standard unit of measurement for the maximum number of reads/writes to noncontiguous storage locations. IOPS is pronounced EYE-OPS. Simply put, IOPS is a measure of a storage device’s read/write speed. It refers to the number of input/output (I/O) operations the device […]
A cyberattack has disrupted operations at one of the world’s biggest boat sellers, the company said in regulatory filings this week. MarineMax, which calls itself the world’s largest recreational boat, yacht, and superyacht services company, filed documents with the Securities and Exchange Commission on Tuesday afternoon describing the incident, which began Sunday. “MarineMax determined… that […]
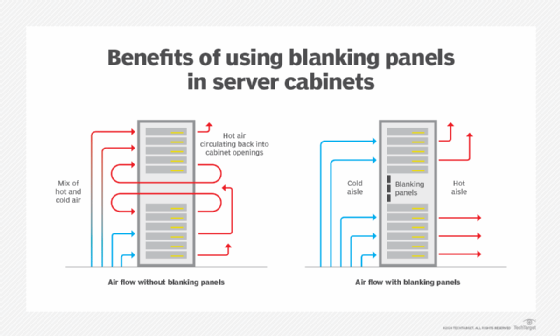
Advancements in modern data center operations lead to new capabilities and management challenges. Recent changes to modern data center standards and design maximize both operational and energy efficiency. The modern data center is far more sophisticated than its predecessors. With proper maintenance and management, today’s data centers can support new generations of hardware for years […]
Processing alerts quickly and efficiently is the cornerstone of a Security Operations Center (SOC) professional’s role. Threat intelligence platforms can significantly enhance their ability to do so. Let’s find out what these platforms are and how they can empower analysts. The Challenge: Alert Overload The modern SOC faces a relentless barrage of security alerts generated […]
A data center is the technological hub of modern enterprise operations. The data center provides the critical IT infrastructure needed to deliver resources and services to business employees, partners and customers around the world. A small or midsize business can often implement a useful “data center” within the confines of a closet or other convenient […]
China has escalated its media campaign alleging US hacking operations, following condemnation from the US, UK and EU in July 2021 over Chinese cyber activities. According to a report published by cybersecurity experts at SentinelLabs today, this offensive strategy involves cooperation between Chinese cybersecurity firms, government agencies and state media to amplify accusations against the […]
The cyberattack led to disruption in Clorox’s business operations, requiring expenses for IT recovery, forensic experts, and professional services to investigate and remediate the attack.
A malware attack can cause security breaches, shut down company operations for extended periods, destroy hardware and cost the company money to fix infected equipment and to remove the virus. Even popular servers like Linux, which does not have virus protection software through Red Hat, are prone to attacks. Malware often enters a system undetected. […]