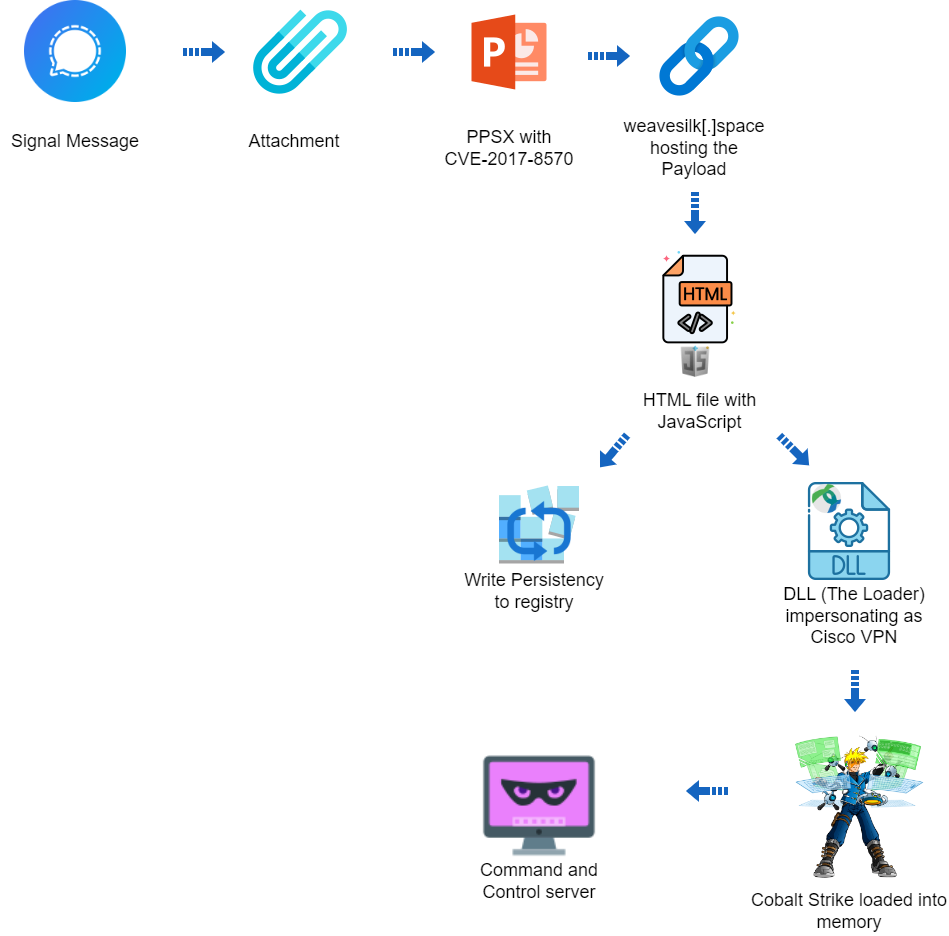
Apr 27, 2024NewsroomCyber Attack / Malware Cybersecurity researchers have discovered a targeted operation against Ukraine that has been found leveraging a nearly seven-year-old flaw in Microsoft Office to deliver Cobalt Strike on compromised systems. The attack chain, which took place at the end of 2023 according to Deep Instinct, employs a PowerPoint slideshow file (“signal-2023-12-20-160512.ppsx”) […]
Executive Summary The Deep Instinct Threat Lab discovered a suspected targeted operation against Ukraine The operation is using CVE-2017-8570 as the initial vector The operation could not be attributed to any known threat actor The operation used a custom loader for Cobalt Strike Beacon Deep Instinct is detecting all stages of the attack Campaign Overview […]
An operator of the HelloKitty ransomware operation announced they changed the name to ‘HelloGookie,’ releasing passwords for previously leaked CD Projekt source code, Cisco network information, and decryption keys from old attacks.
Insikt Group examines a large-scale Russian-language cybercrime operation using fake Web3 gaming initiatives to distribute malware designed to steal information from both macOS and Windows users. These Web3 games, which are based on blockchain technology, offer the potential for financial gains through cryptocurrency earnings. Web of Deceit: The Rise of Imitation Web3 Gaming Scams and […]
What is a context switch? A context switch is an operation that a computer’s central processing unit (CPU) carries out when alternating between processes or threads while ensuring that the processes do not conflict. Effective context switching makes it possible to support a multitasking environment. Each time the CPU makes a switch, the system temporarily […]
The threat actors behind the LockBit ransomware operation have resurfaced on the dark web using new infrastructure, days after an international law enforcement exercise seized control of its servers. To that end, the notorious group has moved its data leak portal to a new .onion address on the TOR network, listing 12 new victims as […]
Feb 02, 2024NewsroomCyber Crime / Malware An INTERPOL-led collaborative operation targeting phishing, banking malware, and ransomware attacks has led to the identification of 1,300 suspicious IP addresses and URLs. The law enforcement effort, codenamed Synergia, took place between September and November 2023 in an attempt to blunt the “growth, escalation and professionalization of transnational cybercrime.” […]
Jan 30, 2024NewsroomCyber Crime / Malware A Brazilian law enforcement operation has led to the arrest of several Brazilian operators in charge of the Grandoreiro malware. The Federal Police of Brazil said it served five temporary arrest warrants and 13 search and seizure warrants in the states of São Paulo, Santa Catarina, Pará, Goiás, and […]
A well-designed operation is using a version of the infamous Mirai malware to secretly distribute cryptocurrency mining software, researchers said Wednesday. Calling it NoaBot, researchers at Akamai said the campaign has been active for about a year, and it has various quirks that complicate analysis of the malware and point to highly-skilled threat actors. The […]