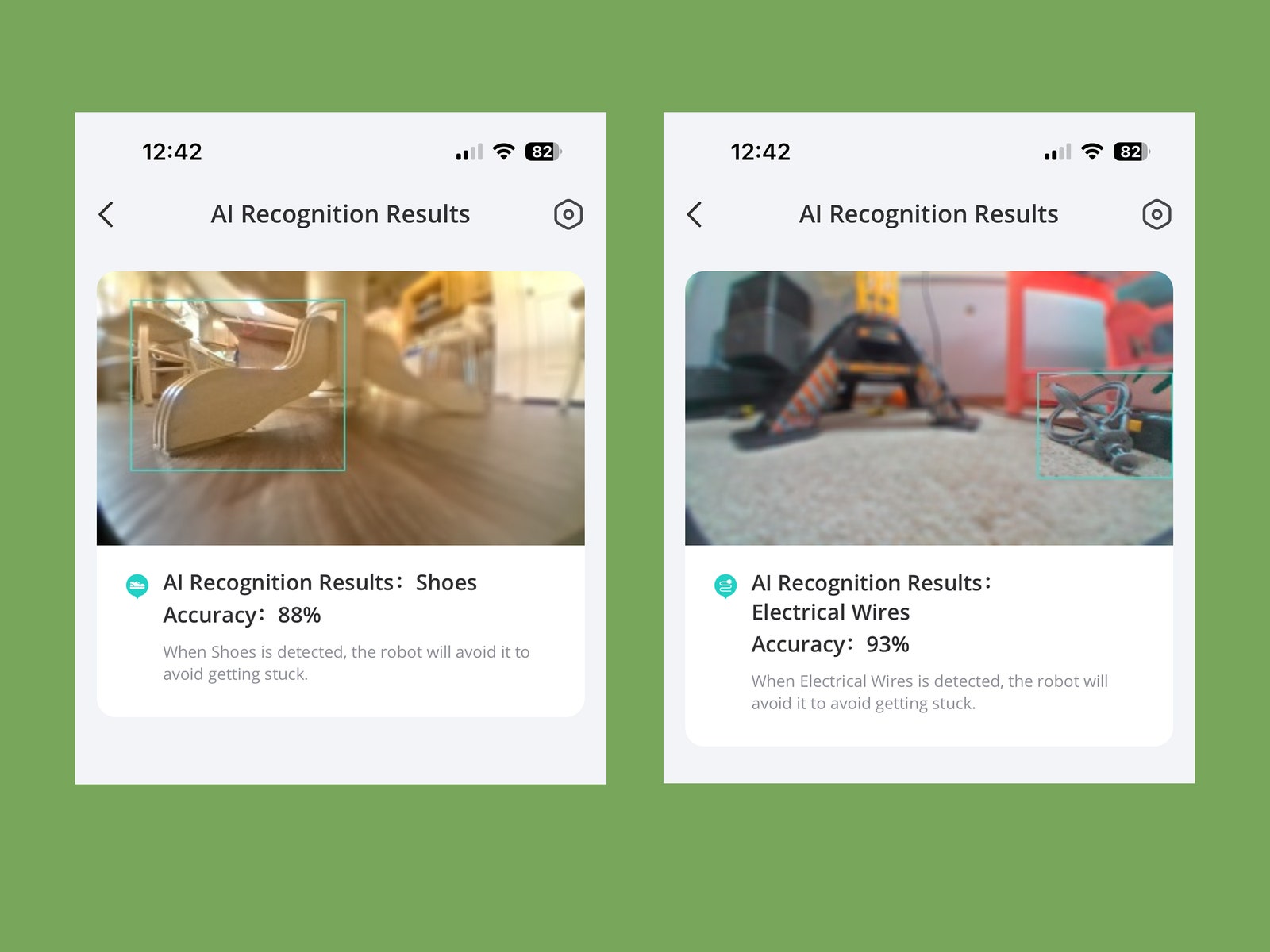
Like last year’s model, it also meets the TÜV Rheinland privacy and security certification. This is important, because it navigates via AI.See—a “visual recognition technology.” Basically, it uses a camera to steer around your house. It’s not upward-facing, and Eufy assures its customers that the photos are not stored in a server and are deleted […]
What is GNOME (GNU Network Object Model Environment)? GNOME (GNU Network Object Model Environment) is a graphical user interface (GUI) and set of computer desktop applications for Linux operating system (OS) users. It’s intended to make a Linux OS easy to use for nonprogrammers. GNOME generally corresponds to the Windows desktop interface and its most […]
Sennheiser’s new flagship studio model aims to strike a balance between neutrality, engagement and comfort. Greg Scarth sits down for some critical listening. Like so many things in life, headphones are all about balance. Aside from the obvious compromise between accurate and engaging sound, manufacturers are trying to balance comfort with weight, all while keeping […]
Mar 13, 2024NewsroomLarge Language Model / AI Security Google’s Gemini large language model (LLM) is susceptible to security threats that could cause it to divulge system prompts, generate harmful content, and carry out indirect injection attacks. The findings come from HiddenLayer, which said the issues impact consumers using Gemini Advanced with Google Workspace as well […]
What is on-demand computing (ODC)? On-demand computing (ODC) is a delivery model in which computing resources are made available to the user as needed. The resources might be maintained within the user’s enterprise or made available by a cloud service provider. The on-demand business computing model was developed to overcome the challenge of enterprises meeting […]
What is a consumption-based pricing model? A consumption-based pricing model is a service provision and payment scheme in which customers pay according to the resources they use. The charges are based on one or more metrics that are measured in units such as the number of application programming interface (API) calls or the amount of […]
Access-as-a-service (AaaS), a new business model in the underground world of cybercrime, refers to threat actors selling methods for accessing networks for a one-time fee. We have one group of criminals, referred to as an access broker or initial access broker (IAB), stealing enterprise user credentials to sell to other attack groups. The buyers then […]
AlphaLock’s business model represents a new and sophisticated approach to cybercrime, creating a pipeline of trained hackers and monetizing their services through an affiliate program.
Nov 02, 2023NewsroomEndpoint Security / Malware As many as 34 unique vulnerable Windows Driver Model (WDM) and Windows Driver Frameworks (WDF) drivers could be exploited by non-privileged threat actors to gain full control of the devices and execute arbitrary code on the underlying systems. “By exploiting the drivers, an attacker without privilege may erase/alter firmware, […]
- 1
- 2