The security issue could lead to the exfiltration of process memory addresses, which could help attackers bypass protection mechanisms like Address Space Layout Randomization (ASLR).
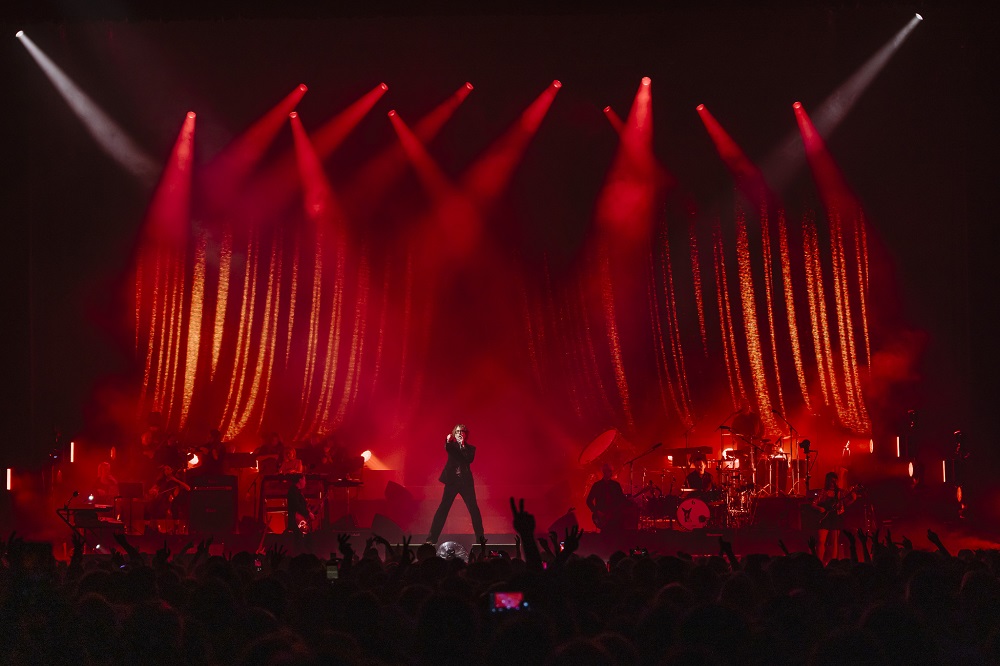
Gigs are dedicated to memory of late bassist Steve Mackey Pulp will play their first North American shows in over a decade as they announce a tour of the US and Canada for this fall. The Sheffield band last performed on the continent in 2012, their final show coming at the Coachella Festival that year […]
CISA adds Apple iOS and iPadOS memory corruption bugs to its Known Exploited Vulnerabilities Catalog
CISA adds Apple iOS and iPadOS memory corruption bugs to its Known Exploited Vulnerabilities Catalog Pierluigi Paganini March 07, 2024 U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds Apple iOS and iPadOS memory corruption vulnerabilities to its Known Exploited Vulnerabilities catalog. The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added the following vulnerabilities to its Known Exploited Vulnerabilities […]
What is RAM (random access memory)? Random access memory (RAM) is the hardware in a computing device that provides temporary storage for the operating system (OS), software programs and any other data in current use so they’re quickly available to the device’s processor. RAM is often referred to as a computer’s main memory, as opposed […]
The maintainers of the cURL data transfer project on Wednesday rolled out patches for a severe memory corruption vulnerability that exposes millions of enterprise OSes, applications and devices to malicious hacker attacks. According to an high-risk bulletin, the flaw poses a direct threat to the SOCKS5 proxy handshake process in cURL and can be exploited […]
The Cybersecurity and Infrastructure Security Agency is urging the software industry to embrace the use of memory safe programming languages as part of a wider effort to eliminate security vulnerabilities in code. CISA called for the changes alongside a push to embrace secure-by-design practices during the software development stage and to increase the security of […]
Sep 14, 2023THNEndpoint Security / Vulnerability A set of memory corruption flaws have been discovered in the ncurses (short for new curses) programming library that could be exploited by threat actors to run malicious code on vulnerable Linux and macOS systems. “Using environment variable poisoning, attackers could chain these vulnerabilities to elevate privileges and run […]