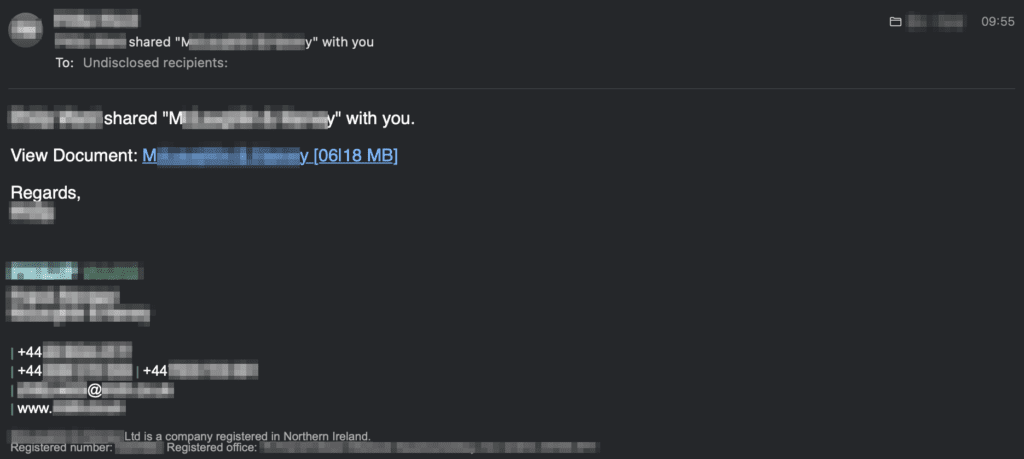
Autodesk is hosting malicious PDF files that lead phishing attack victims to have their Microsoft login credentials stolen. The elaborate phishing campaign behind these attacks is much more convincing than normal, as it uses compromised email accounts to find and attack new targets. These accounts are used to send phishing emails to existing contacts, using […]
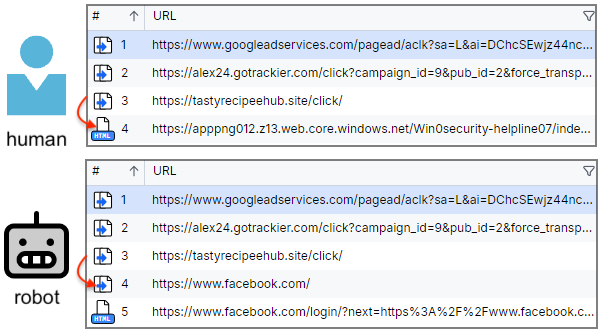
Today, we are looking at a malicious ad campaign targeting Facebook users via Google search. It is well-known that tech support scammers attract new victims by buying ads for certain keywords related to their audience. What is perhaps less known is how it is even possible to impersonate top brands and get away with it. […]
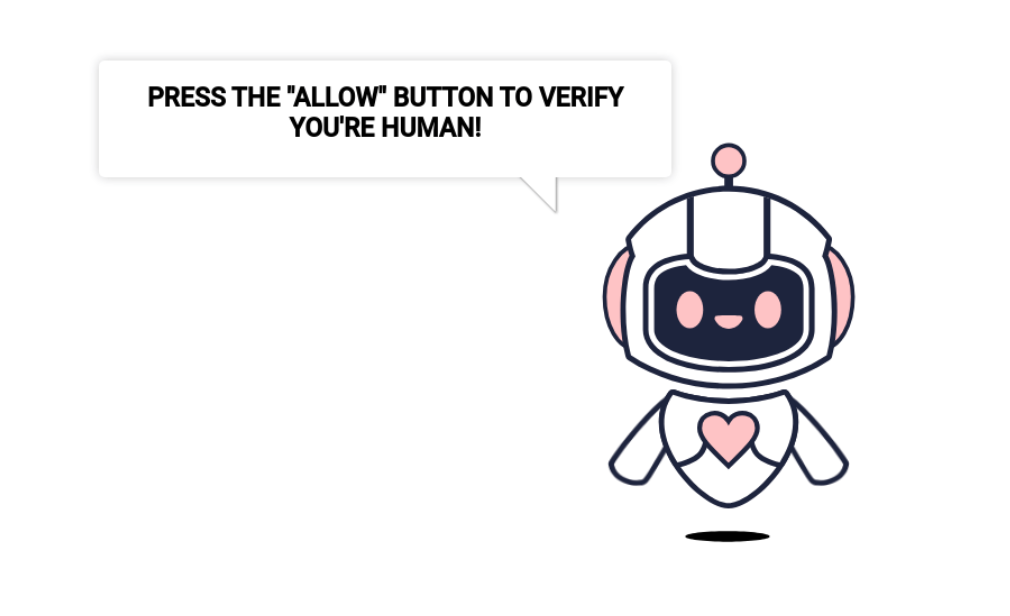
Last August we documented a malware campaign that was injecting malicious JavaScript code into compromised WordPress sites to redirect site visitors to VexTrio domains. The most interesting thing about that malware was how it used dynamic DNS TXT records of the tracker-cloud[.]com domain to obtain redirect URLs. Typical notification scam destination for the redirects We’ve […]
Sandboxes are synonymous with dynamic malware analysis. They help to execute malicious files in a safe virtual environment and observe their behavior. However, they also offer plenty of value in terms of static analysis. See these five scenarios where a sandbox can prove to be a useful tool in your investigations. Detecting Threats in PDFs […]
The attacks begin with malicious emails containing seemingly innocuous document attachments (Excel and Word files) that exploit the CVE-2017-11882 flaw, a commonly targeted Microsoft Office Equation Editor vulnerability fixed in 2017.
Most of the malicious search ads we have seen have originated from Google, but threat actors are also abusing other search engines. Microsoft Bing is probably the second best target due to its close ties to the Windows ecosystem and Edge browser. In this blog post, we look at a very recent malvertising campaign impersonating […]
PikaBot, along with other malicious loaders like QBot and DarkGate, heavily depends on spam campaigns for distribution. Its initial access strategies are intricately crafted, utilizing geographically targeted spam emails for specific countries.
The malicious code inserted into the open-source library XZ Utils, a widely used package present in major Linux distributions, is also capable of facilitating remote code execution, a new analysis has revealed. The audacious supply chain compromise, tracked as CVE-2024-3094 (CVSS score: 10.0), came to light last week when Microsoft engineer and PostgreSQL developer Andres […]
Apr 01, 2024NewsroomBotnet / Mobile Security Several malicious Android apps that turn mobile devices running the operating system into residential proxies (RESIPs) for other threat actors have been observed on the Google Play Store. The findings come from HUMAN’s Satori Threat Intelligence team, which said the cluster of VPN apps came fitted with a Golang […]