Autodesk is hosting malicious PDF files that lead phishing attack victims to have their Microsoft login credentials stolen. The elaborate phishing campaign behind these attacks is much more convincing than normal, as it uses compromised email accounts to find and attack new targets. These accounts are used to send phishing emails to existing contacts, using […]
The security issue could lead to the exfiltration of process memory addresses, which could help attackers bypass protection mechanisms like Address Space Layout Randomization (ASLR).
Newly discovered HTTP/2 protocol vulnerabilities called “CONTINUATION Flood” can lead to denial of service (DoS) attacks, crashing web servers with a single TCP connection in some implementations.
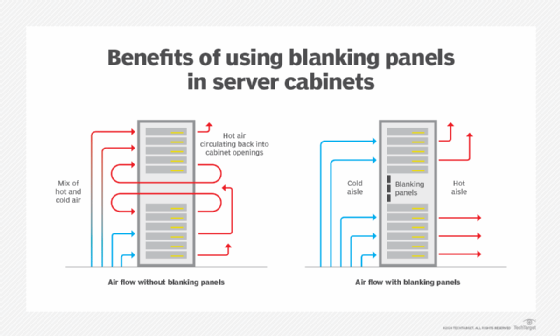
Advancements in modern data center operations lead to new capabilities and management challenges. Recent changes to modern data center standards and design maximize both operational and energy efficiency. The modern data center is far more sophisticated than its predecessors. With proper maintenance and management, today’s data centers can support new generations of hardware for years […]
The vulnerabilities impact devices with default configurations and can lead to system configuration modifications, creation of privileged accounts, and denial of service conditions.
Hear the ‘Klub Romance’ EP’s lead track right here Gratts is back once again, hot on the heels of various Balearic outings like ‘Sun Circles’, ‘Pretty Lights’ and ‘Jour De Fete’ but this time he is in house mode. This release comes under his new Trackhead T moniker and finds him keeping things raw and […]
One of the vulnerabilities, known as “Reptar,” affects Intel CPUs and could lead to system instability or privilege escalation. The other vulnerability, CVE-2023-46835, could allow malicious code in a guest VM to compromise an AMD-based host.