The cyber threat actor known as NoName057(16) has been observed changing tactics amid the escalating conflict between Ukraine and Russia. The group has gained notoriety for their involvement in Project DDoSia, an initiative aimed at executing large-scale distributed denial-of-service (DDoS) attacks against entities supporting Ukraine, predominantly NATO member states. Sekoia.io, a cybersecurity monitoring platform, has been […]
Mar 05, 2024NewsroomEmail Security / Network Security The threat actor known as TA577 has been observed using ZIP archive attachments in phishing emails with an aim to steal NT LAN Manager (NTLM) hashes. The new attack chain “can be used for sensitive information gathering purposes and to enable follow-on activity,” enterprise security firm Proofpoint said […]
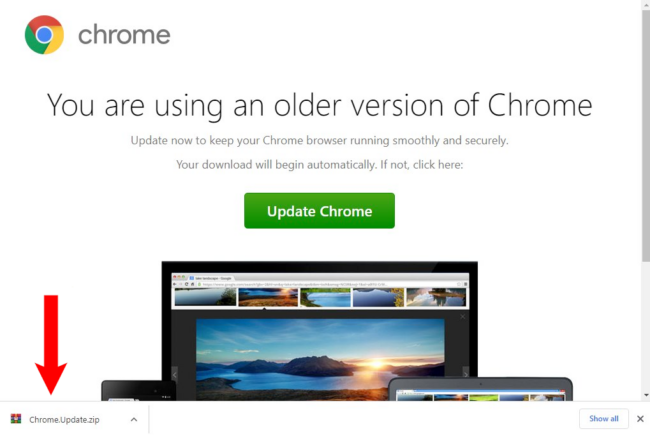
SocGholish malware, otherwise known as “fake browser updates”, is one of the most common types of malware infections that we see on hacked websites. This long-standing malware campaign leverages a JavaScript malware framework that has been in use since at least 2017. The malware attempts to trick unsuspecting users into downloading what is actually a […]
CISA adds Microsoft Streaming Service bug to its Known Exploited Vulnerabilities catalog Pierluigi Paganini March 01, 2024 U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds a Microsoft Streaming Service vulnerability to its Known Exploited Vulnerabilities catalog. The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added the CVE-2023-29360 (CVSS Score 8.4) Microsoft Streaming Service Untrusted pointer dereference vulnerability […]
Feb 28, 2024NewsroomCyber Espionage / Malware An Iran-nexus threat actor known as UNC1549 has been attributed with medium confidence to a new set of attacks targeting aerospace, aviation, and defense industries in the Middle East, including Israel and the U.A.E. Other targets of the cyber espionage activity likely include Turkey, India, and Albania, Google-owned Mandiant […]
Portland activist and DJ gets active behind the decks Portland-based artist C Powers, also known as Cecilia Powers, is not only a skilled producer and DJ but also a dedicated tenants’ rights activist. Her work straddles both passions and reflects her commitment to community organising and intersectionality, embodying the essence of a “community in motion”. Whether […]
A containerized data center, also known as a modular data center, is a data center within a container. For companies that need to increase IT capacity quickly, affordably and temporarily, containerized data centers are a great option, and customized modular data centers can more permanently scale services and support. The “container” can vary, including a […]
Feb 14, 2024NewsroomMalware / Cybercrime The infamous malware loader and initial access broker known as Bumblebee has resurfaced after a four-month absence as part of a new phishing campaign observed in February 2024. Enterprise security firm Proofpoint said the activity targets organizations in the U.S. with voicemail-themed lures containing links to OneDrive URLs. “The URLs […]
The XLoader Android malware, operated by the threat actor known as Roaming Mantis, has been found to automatically execute on infected devices without requiring user interaction.