Cisco warns of a command injection escalation flaw in its IMC. PoC publicly available Pierluigi Paganini April 18, 2024 Cisco has addressed a high-severity vulnerability in its Integrated Management Controller (IMC) for which publicly available exploit code exists. Cisco has addressed a high-severity Integrated Management Controller (IMC) vulnerability and is aware of a public exploit […]
According to Silicon Angle, this significant injection of capital is spearheaded by Altimeter Capital Management LP, with notable participation from Point72 Ventures LLC, marking a new milestone for the company founded in 2020.
Fortinet patched a critical SQL injection vulnerability (CVE-2023-48788) in its FortiClient EMS software, allowing unauthenticated attackers to achieve remote code execution with SYSTEM privileges.
Three vulnerabilities have been disclosed, including an authentication bypass, command injection, and SQL injection, with one allowing remote execution without authentication.
The vulnerabilities, CVE-2023-50358 and CVE-2023-47218, are command injection flaws in the QTS firmware, with potential for remote code execution, impacting a large number of devices globally.
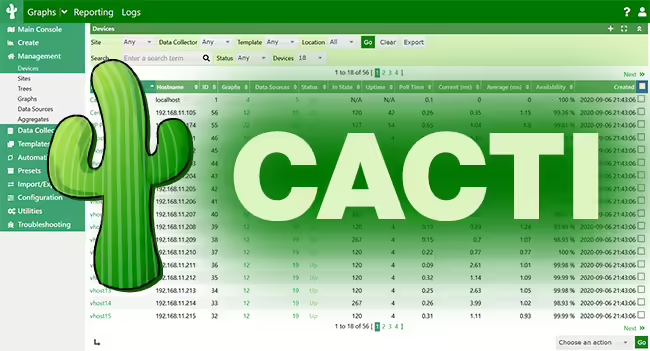
A blind SQL injection vulnerability (CVE-2023-51448) in Cacti, a widely-used network monitoring, performance and fault management framework, could lead to information disclosure and potentially remote code execution. Cacti is often used in network operation centers of telecoms and web hosting providers, to collect network performance data and store it in RRDtool, a logging and graphing […]
A threat actor named “xc7d2f4” is allegedly selling remote command injection vulnerability for Cisco ASA. The threat actor has claimed that this vulnerability exists on all 55XX series of the Cisco Adaptive Security Appliance (ASA). The Cyber Express has reached out to Cisco to confirm the details of the alleged vulnerability exposure, but an official […]
Prompt injection is, thus far, an unresolved challenge that poses a significant threat to Language Model (LLM) integrity. This risk is particularly alarming when LLMs are turned into agents that interact directly with the external world, utilizing tools to fetch data or execute actions. Malicious actors can leverage prompt injection techniques to generate unintended and […]
Dec 11, 2023NewsroomEndpoint Security / Malware A new collection of eight process injection techniques, collectively dubbed PoolParty, could be exploited to achieve code execution in Windows systems while evading endpoint detection and response (EDR) systems. SafeBreach researcher Alon Leviev said the methods are “capable of working across all processes without any limitations, making them more […]
- 1
- 2