Jan 26, 2024NewsroomMalvertising / Phishing-as-a-service Chinese-speaking users have been targeted by malicious Google ads for restricted messaging apps like Telegram as part of an ongoing malvertising campaign. “The threat actor is abusing Google advertiser accounts to create malicious ads and pointing them to pages where unsuspecting users will download Remote Administration Trojan (RATs) instead,” Malwarebytes’ […]
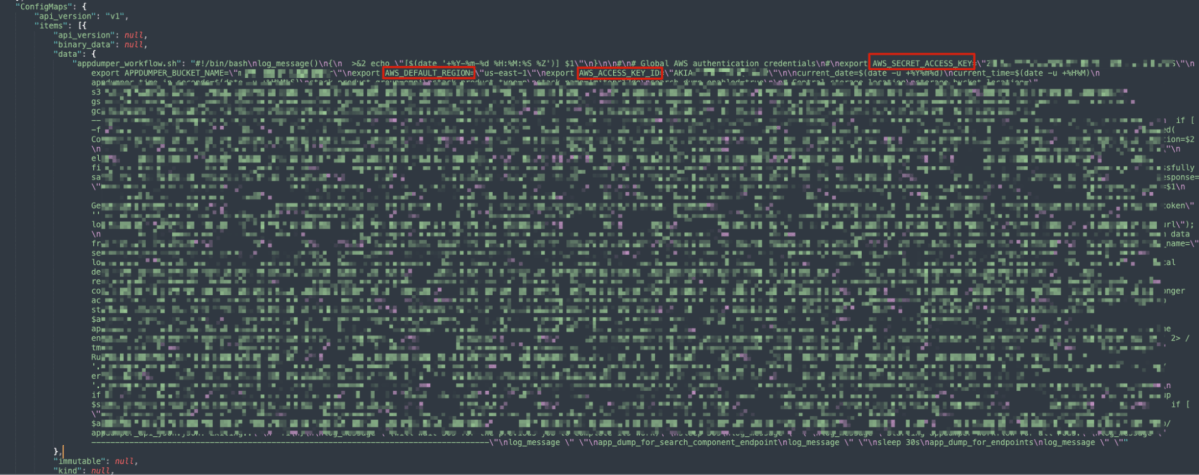
Following our discovery of a critical loophole in Google Kubernetes Engine (GKE) dubbed Sys:All, we decided to conduct research into the real-world impacts of this issue. Our initial probe already revealed over a thousand vulnerable GKE clusters due to admins configuring RBAC bindings making the system:authenticated group overprivileged, which could potentially allow any Google account […]
Jan 24, 2024NewsroomCloud Security / Kubernetes Cybersecurity researchers have discovered a loophole impacting Google Kubernetes Engine (GKE) that could be potentially exploited by threat actors with a Google account to take control of a Kubernetes cluster. The critical shortcoming has been codenamed Sys:All by cloud security firm Orca. As many as 250,000 active GKE clusters […]
Users are recommended to switch to the mobile versions available on iOS and Google Play. The decision to sunset the desktop app is part of Twilio’s effort to focus on areas with higher demand.
Google downplays the severity of the issue, treating it as regular cookie theft and suggesting users log out of their Chrome browser to invalidate the stolen cookies and tokens.
DriveFS Sleuth automates the investigation of Google Drive File Stream disk artifacts. The tool can parse the disk artifacts and build a filesystem tree-like structure enumerating the synchronized files along with their respective properties. “While engaged in a threat-hunting activity for a client to detect the misuse of file-syncing applications within their network, I identified […]
The Twitter account of cybersecurity firm Mandiant, which is owned by Google, was hacked and used to promote a cryptocurrency scam. The attacker impersonated the Phantom crypto wallet and shared a fake website offering free tokens.
The CISA has identified two recently patched vulnerabilities, one in Google Chrome and another in the open-source Perl library Spreadsheet::ParseExcel, that have been actively exploited and require immediate mitigation.
The end of support for these older Windows versions is due to the reliance on an embedded version of Google Chrome that no longer functions on them, as well as the need for Windows feature and security updates only available on Windows 10 and above.