Oops, your XML now contains shell code The following XML code was found in the layout_update database table and is responsible for periodic reinfections of your system. Attackers combine the Magento layout parser with the beberlei/assert package (installed by default) to execute system commands. Because the layout block is tied to the checkout cart, this […]
The first 72 hours after LockBit’s disruption In the days following the disruption, the topic was still being widely discussed across underground forums. Members of the forums seemed to appreciate the NCA’s sense of humor, commenting that the law enforcement agency was trying to be “lulzy” (internet slang for comical or amusing) in its actions […]
Technical Analysis The following analysis covers the technical characteristics of Case Study 1 and Case Study 2 for Tweaks. Case Study 1 1. BAT files establish webhooks: To start, once the user downloads the BAT file and executes it, the malware establishes the necessary webhook URLs using the Powershell commands below: “$payload = [PSCustomObject]@{ embeds […]
Bumblebee malware has re-emerged following a four-month absence from the cyber threat landscape, according to Proofpoint research. The new campaign, observed in February 2024, used a “significantly different” attack chain compared to previous Bumblebee infiltrations. The return of Bumblebee coincides with the reappearance of several notorious threat actors at the start of 2024 following a […]
China has escalated its media campaign alleging US hacking operations, following condemnation from the US, UK and EU in July 2021 over Chinese cyber activities. According to a report published by cybersecurity experts at SentinelLabs today, this offensive strategy involves cooperation between Chinese cybersecurity firms, government agencies and state media to amplify accusations against the […]
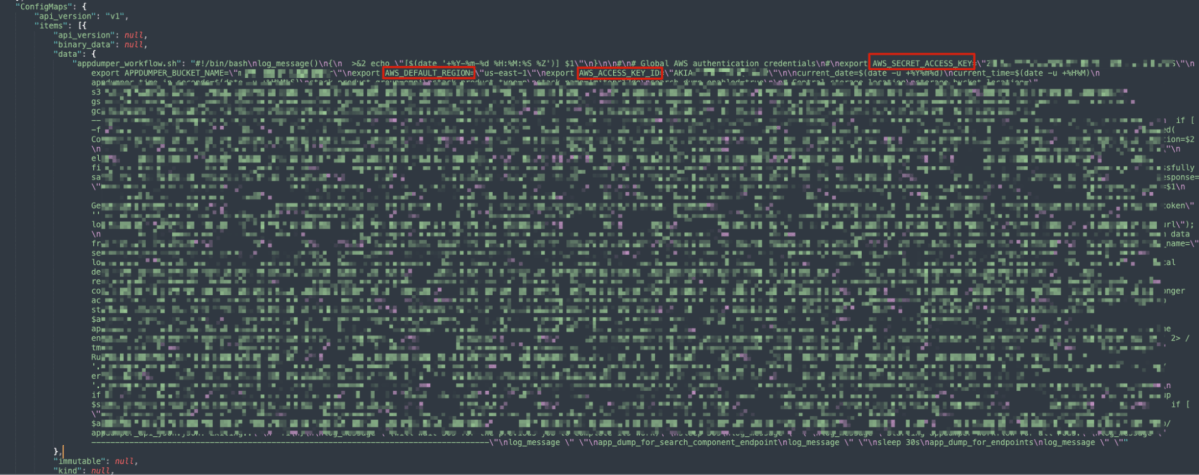
Following our discovery of a critical loophole in Google Kubernetes Engine (GKE) dubbed Sys:All, we decided to conduct research into the real-world impacts of this issue. Our initial probe already revealed over a thousand vulnerable GKE clusters due to admins configuring RBAC bindings making the system:authenticated group overprivileged, which could potentially allow any Google account […]
Technical Analysis In the following sections, we dive into the technical details surrounding Zloader’s new updates to their anti-analysis techniques, embedded configuration, DGA, and network encryption. Anti-analysis techniques Zloader uses a combination of API import hashing, junk code, a filename check, and string obfuscation. The following sections analyze each technique. Imports and API resolution The […]
Small business owners have been left feeling suicidal following ransomware attacks, according to new research that examines how the criminal ecosystem is causing harm beyond simply the money it extorts from victims. The new report from the Royal United Services Institute (RUSI) creates a typology of harm for ransomware, including the “significantly overlooked” psychological impact […]
The websites and online services for multiple Chambers of Crafts in Germany are down following a “security incident” that appears to have impacted a managed service provider. A statement on the parent organization’s website, which is still online, says that the cyberattack affected an unidentified IT service’s data center and was discovered during the first […]