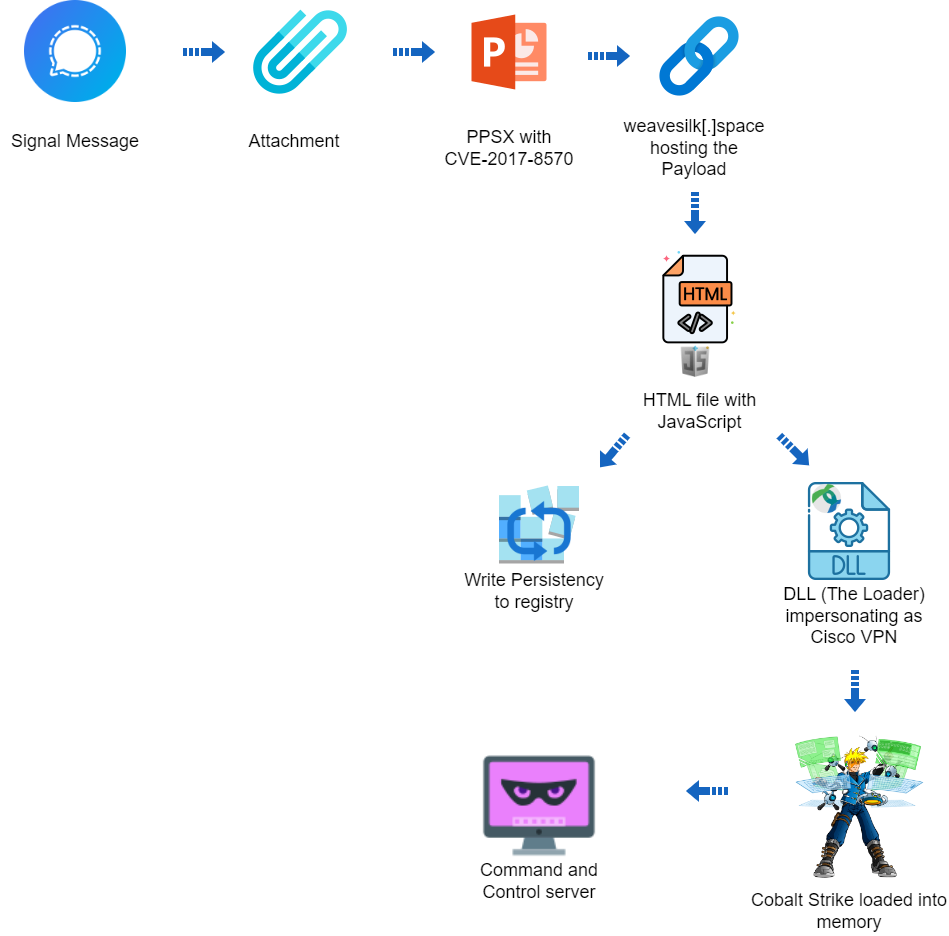
Executive Summary The Deep Instinct Threat Lab discovered a suspected targeted operation against Ukraine The operation is using CVE-2017-8570 as the initial vector The operation could not be attributed to any known threat actor The operation used a custom loader for Cobalt Strike Beacon Deep Instinct is detecting all stages of the attack Campaign Overview […]
U.S. President Joe Biden has issued an Executive Order that prohibits the mass transfer of citizens’ personal data to countries of concern. The Executive Order also “provides safeguards around other activities that can give those countries access to Americans’ sensitive data,” the White House said in a statement. This includes sensitive information such as genomic […]
The White House issued an executive order on Wednesday that is designed to improve maritime port security by creating new requirements for stronger cyberdefenses in the sector while expanding the authorities of the U.S. Coast Guard to respond to cybersecurity incidents. The Biden administration said the executive order will force the sector to bolster its […]
Executive summary AT&T Alien Labs has identified a campaign to deliver AsyncRAT onto unsuspecting victim systems. During at least 11 months, this threat actor has been working on delivering the RAT through an initial JavaScript file, embedded in a phishing page. After more than 300 samples and over 100 domains later, the threat actor is […]
Jan 04, 2024The Hacker NewsEthical Hacking / Vulnerability Assessment Section four of the “Executive Order on Improving the Nation’s Cybersecurity” introduced a lot of people in tech to the concept of a “Software Supply Chain” and securing it. If you make software and ever hope to sell it to one or more federal agencies, you […]
Executive summary In recent developments, a sophisticated malware stealer strain crafted in the Go programming language has been discovered by AT&T Alien Labs, posing a severe threat to both Windows and macOS operating systems. As of the time of publishing of this article, traditional antivirus solutions have low or even non-existent detection rates, making it […]
In a blog post on Dec. 5, Microsoft executive vice president of security Charlie Bell announced that as part of its new strategic focus on security, the company will shift Bret Arsenault out of his longtime role as CISO and into a chief security adviser position. In his place, Igor Tsyganskiy will assume the CISO […]
Executive Summary Unit 42 researchers observed a series of apparently related attacks against organizations in the Middle East, Africa and the U.S. We will discuss a set of tools used in the course of the attacks that reveal clues about the threat actors’ activity. We are sharing this research to provide detection, prevention and hunting […]
Over the Kazuar’s Nest: Cracking Down on a Freshly Hatched Backdoor Used by Pensive Ursa (Aka Turla)
Executive Summary While tracking the evolution of Pensive Ursa (aka Turla, Uroburos), Unit 42 researchers came across a new, upgraded variant of Kazuar. Not only is Kazuar another name for the enormous and dangerous cassowary bird, Kazuar is an advanced and stealthy .NET backdoor that Pensive Ursa usually uses as a second stage payload. Pensive […]
- 1
- 2