The clearnet domain of the notorious BreachForums data leak and hacking forum has been taken down by rival threat actors. The threat actor group, R00TK1T, along with the pro-Russian gang Cyber Army of Russia, announced a breach of user data following the BreachForums take down. R00TK1T was previously responsible for an attack campaign targeting the […]
Scammers are using fake news campaigns and cheaply acquired domain names to sell dubious health products, often claiming endorsements from popular entrepreneurial reality shows like Shark Tank and Dragons’ Den.
The botnet uses a domain generation algorithm (DGA) to connect with its command and control server and can be instructed to establish backconnect server connections, allowing infected devices to be used as proxy servers.
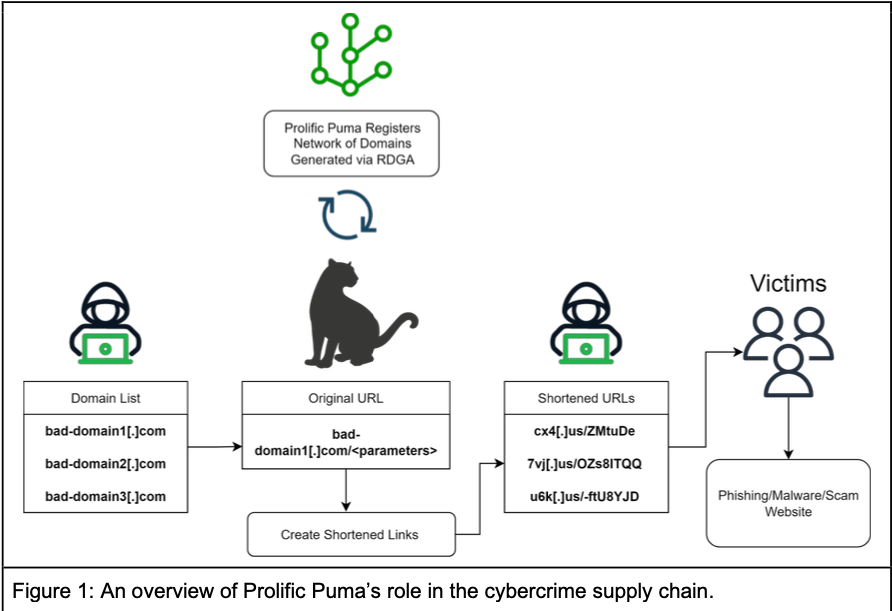
The top-level domain for the United States — .US — is home to thousands of newly-registered domains tied to a malicious link shortening service that facilitates malware and phishing scams, new research suggests. The findings come close on the heels of a report that identified .US domains as among the most prevalent in phishing attacks […]
Royal gained access to the City’s network using a stolen domain service account in early April and maintained access to the compromised systems between April 7 and May 4.
Researchers at Akamai have unearthed a concerning shift in the behavior of dynamically seeded Domain Generation Algorithm (DGA) families within Domain Name System (DNS) traffic data. This discovery reveals how malicious actors are adapting their tactics to prolong the life of their command-and-control (C2) communication channels, safeguarding their botnets. From a technical standpoint, DGAs come […]