The smart home doesn’t always feel smart. I test a lot of devices for a living, and they take a lot of babysitting and steps to do everything you want. Whether you’re setting up skills on an Alexa speaker or getting your smart lights on the right schedule–shout-out to Daylight Savings for ruining my existing […]
Chinese and Russian hackers have turned their focus to edge devices — like VPN appliances, firewalls, routers and Internet of Things (IoT) tools — amid a startling increase in espionage attacks, according to Google security firm Mandiant. The company published the findings as part of its annual report on cyber investigations Mandiant was involved in […]
Siemens is urging organizations using its Ruggedcom APE1808 devices configured with Palo Alto Networks (PAN) Virtual NGFW to implement workarounds for a maximum severity zero-day bug that PAN recently disclosed in its next-gen firewall product. The command injection vulnerability, identified as CVE-2024-3400, affects multiple versions of PAN-OS firewalls when certain features are enabled on them. […]
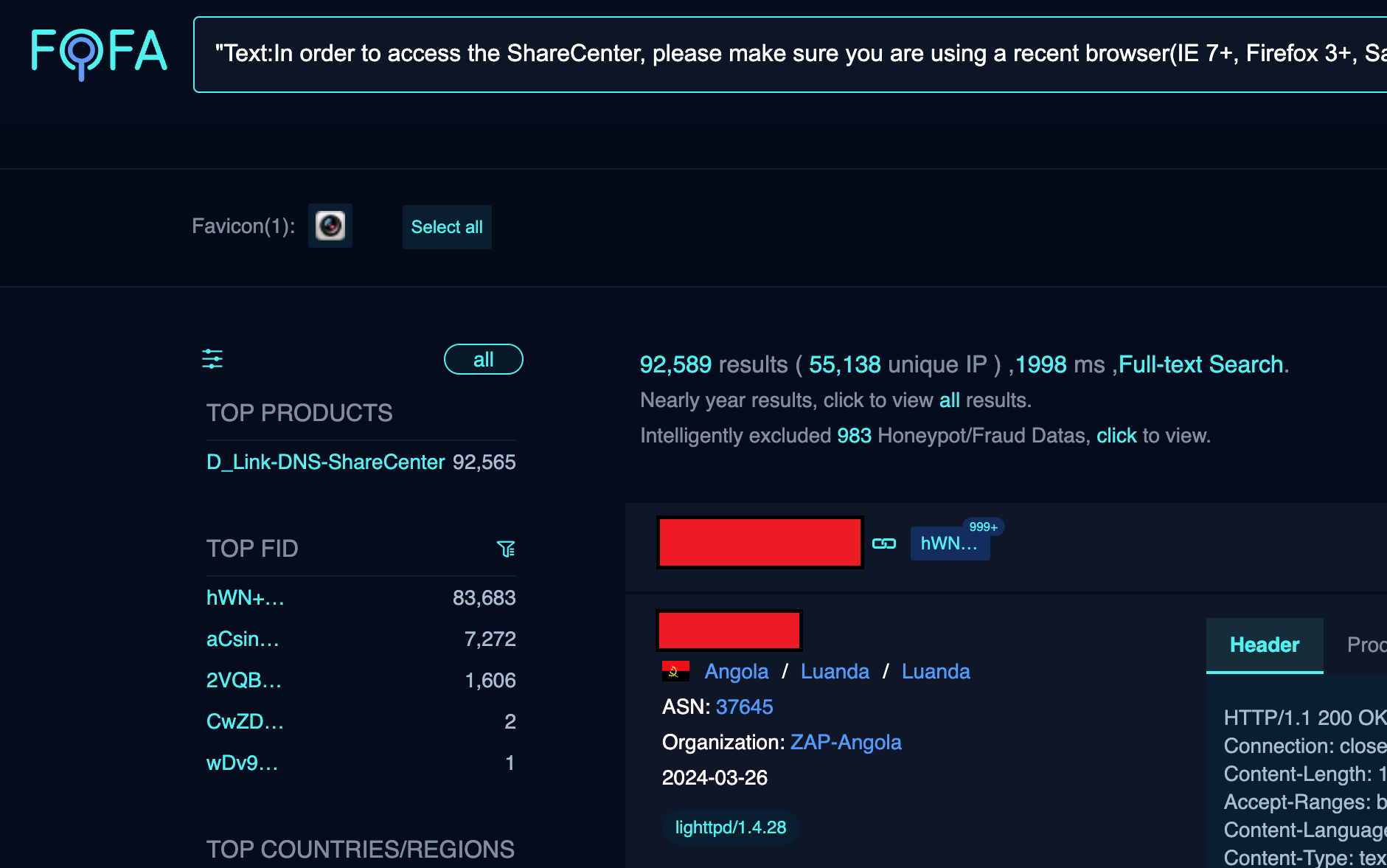
Over 92,000 Internet-facing D-Link NAS devices can be easily hacked Pierluigi Paganini April 07, 2024 A researcher disclosed an arbitrary command injection and hardcoded backdoor issue in multiple end-of-life D-Link NAS models. A researcher who goes online with the moniker ‘Netsecfish’ disclosed a new arbitrary command injection and hardcoded backdoor flaw, tracked as , tracked […]
The vulnerabilities impact devices with default configurations and can lead to system configuration modifications, creation of privileged accounts, and denial of service conditions.
The flaw allows attackers to bypass authentication and access restricted resources on vulnerable devices. The exploitation volume is high, with over 170 distinct IP addresses attempting to exploit the vulnerability.
The code embedded inside devices that bridges interactions between hardware and software is frequently exposed to security vulnerabilities, but lawmakers and federal officials have not paid enough attention to them, a national security think tank analysis argues. The report, released Wednesday by the Foundation for Defense of Democracies, contends that firmware vulnerabilities remain largely unaddressed, […]
The Xamalicious backdoor, implemented with Xamarin, targets Android devices by gaining accessibility privileges and communicating with a C2 server to download a second-stage payload, potentially enabling fraudulent actions without user consent.
The attackers infect victims’ devices and then inject a script onto the victim’s browser to modify webpage content. This new approach makes the attacks more stealthy and harder to detect.