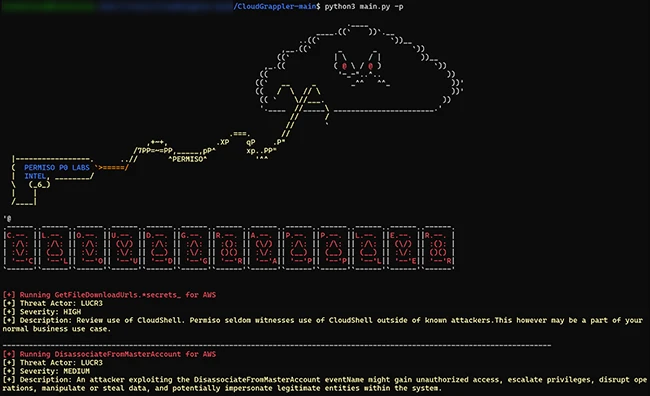
CloudGrappler is an open-source tool designed to assist security teams in identifying threat actors within their AWS and Azure environments. The tool, built on the foundation of Cado Security’s cloudgrep project, offers enhanced detection capabilities based on the tactics, techniques, and procedures (TTPs) of modern cloud threat actors like LUCR-3 (Scattered Spider). CloudGrappler queries for […]
Feb 27, 2024The Hacker NewsMalware / Network Security An “intricately designed” remote access trojan (RAT) called Xeno RAT has been made available on GitHub, making it available to other actors at no extra cost. Written in C# and compatible with Windows 10 and Windows 11 operating systems, the open-source RAT comes with a “comprehensive set […]
The White House issued an executive order on Wednesday that is designed to improve maritime port security by creating new requirements for stronger cyberdefenses in the sector while expanding the authorities of the U.S. Coast Guard to respond to cybersecurity incidents. The Biden administration said the executive order will force the sector to bolster its […]
The new variant, referred to as LockBit-NG-Dev, was being designed to succeed the most recent LockBit 3.0 iteration, using .NET and CoreRT for cross-platform compatibility.
Malware designed to seek out and disable enterprise security defenses has surged in popularity over the past year to comprise nearly a quarter (26%) of all detections in 2023, according to Picus Security. The cybersecurity vendor revealed the news in its Picus Red Report 2024, compiled from analysis of 612,080 malicious files last year, to […]
SiCat is an open-source tool for exploit research designed to source and compile information about exploits from open channels and internal databases. Its primary aim is to assist in cybersecurity, enabling users to search the internet for potential vulnerabilities and corresponding exploits. Akas Wisnu Aji, the creator of SiCat, outlined the key features of the […]
SiCat is an open-source tool for exploit research designed to source and compile information about exploits from open channels and internal databases. Its primary aim is to assist in cybersecurity, enabling users to search the internet for potential vulnerabilities and corresponding exploits. Akas Wisnu Aji, the creator of SiCat, outlined the key features of the […]
The Federal Trade Commission (FTC) is now accepting submissions for a contest designed to spur development of products and policies to protect consumers from the malicious use of voice cloning technology, which has been fueled by the advance of text-to-speech artificial intelligence capabilities. The challenge is an effort by the FTC to speed the evolution […]
AI security researchers from Robust Intelligence and Yale University have designed a machine learning technique that can speedily jailbreak large language models (LLMs) in an automated fashion. “The method, known as the Tree of Attacks with Pruning (TAP), can be used to induce sophisticated models like GPT-4 and Llama-2 to produce hundreds of toxic, harmful, […]