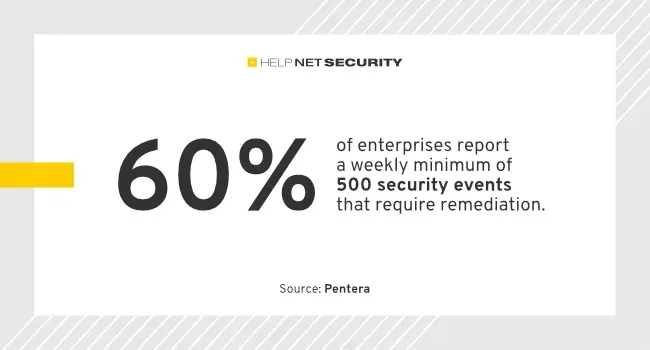
Threat actors are continuing to successfully breach across the entire attack surface and the stakes are only getting higher: 93% of enterprises who admitted a breach reported unplanned downtime, data exposure, or financial loss as a result, according to Pentera. Pentera surveyed 450 CISOs, CIOs, and IT security leaders at enterprise companies with more than […]
Dell Technologies is continuing down the path to AI and cloud by branching out to support more AI accelerators and cloud file storage offerings, potentially relieving supply chain backlogs and giving customers more options. Dell is adding the Intel Gaudi 3 AI accelerator as an option to its PowerEdge XE9680 a few weeks after its […]
Jan 22, 2024NewsroomPrivacy / Technology The U.S. Federal Trade Commission (FTC) is continuing to clamp down on data brokers by prohibiting InMarket Media from selling or licensing precise location data. The settlement is part of allegations that the Texas-based company did not inform or seek consent from consumers before using their location information for advertising […]
Last updated at Mon, 16 Oct 2023 15:02:23 GMT As part of our continuing research project into managed file transfer risk, including JSCAPE MFT and Fortra Globalscape EFT Server, Rapid7 discovered several vulnerabilities in South River Technologies’ Titan MFT and Titan SFTP servers. Although these require unusual circumstances or non-default configurations, as well as a […]
Espionage actors are continuing to mount attacks on critical national infrastructure (CNI) targets, a trend that has become a source of concern for governments and CNI organizations worldwide. Symantec’s Threat Hunter Team has found evidence that a threat actor group Symantec calls Redfly used the ShadowPad Trojan to compromise a national grid in an Asian […]
Sep 08, 2023THNZero Day / Cyber Attack Threat actors associated with North Korea are continuing to target the cybersecurity community using a zero-day bug in unspecified software over the past several weeks to infiltrate their machines. The findings come from Google’s Threat Analysis Group (TAG), which found the adversary setting up fake accounts on social […]