What is a context switch? A context switch is an operation that a computer’s central processing unit (CPU) carries out when alternating between processes or threads while ensuring that the processes do not conflict. Effective context switching makes it possible to support a multitasking environment. Each time the CPU makes a switch, the system temporarily […]
Feb 02, 2024NewsroomNational Security / Data Breach A former software engineer with the U.S. Central Intelligence Agency (CIA) has been sentenced to 40 years in prison by the Southern District of New York (SDNY) for transmitting classified documents to WikiLeaks and for possessing child pornographic material. Joshua Adam Schulte, 35, was originally charged in June […]
The EMBA open-source security analyzer is tailored as the central firmware analysis tool for penetration testers and product security groups. It assists throughout the security evaluation procedure, extracting firmware, conducting static and dynamic analysis through emulation, and creating a web-based report. EMBA features EMBA identifies potential vulnerabilities and weak points in firmware, such as insecure […]
The central bank of southern African country Lesotho is facing severe outages due to a cyberattack that was discovered earlier this week. The bank released multiple statements confirming that a recent incident affected several systems. The landlocked mountainous country is encircled by South Africa and has a population of more than 2 million. “The Central […]
The organization that runs the transit system for central Virginia dealt with a computer network disruption due to a cyberattack around the Thanksgiving holiday. The Greater Richmond Transit Company (GRTC) provides bus and specialized transportation services for millions of people across Richmond, Chesterfield and Henrico Counties. A spokesperson told Recorded Future News that around Thanksgiving […]
Zhang Hongliang, a former restaurant manager in central China, took various gigs in and outside China to support his family after losing his job during the COVID-19 pandemic. In March, a job offer to teach Chinese cooking at a restaurant led him into a cyber scam compound in Myanmar, where he was instead ordered to […]
India’s Central Bureau of Investigation (CBI) conducted raids at 76 locations across the country as part of Operation Chakra-II, targeting cybercrime operations involved in tech support scams and cryptocurrency fraud.
In today’s digital age, where technology plays a central role in every aspect of our lives, organizations in the Asia-Pacific region face an increasingly complex cyber security landscape. To safeguard sensitive information and prevent cyber threats, it is imperative to prioritize cyber security awareness in organizational education, training and development initiatives. The cyber security landscape […]
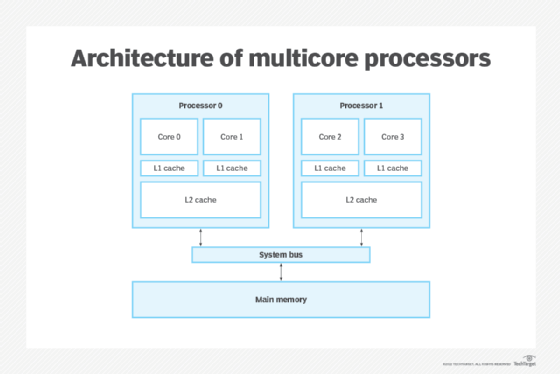
What is multiprocessing? Multiprocessing is the utilization of two or more central processing units (CPUs) in a single computer system. Its definition can vary depending on the context, but generally it refers to a system’s ability to support multiple CPUs and its capacity to distribute work among them. Multicore processors today are easily capable of […]