Apr 23, 2024NewsroomSupply Chain Attack / Application Security Researchers have identified a dependency confusion vulnerability impacting an archived Apache project called Cordova App Harness. Dependency confusion attacks take place owing to the fact that package managers check the public repositories before private registries, thus allowing a threat actor to publish a malicious package with the […]
Apr 17, 2024NewsroomVulnerability / Web Application Firewall Cybersecurity researchers have discovered a new campaign that’s exploiting a recently disclosed security flaw in Fortinet FortiClient EMS devices to deliver ScreenConnect and Metasploit Powerfun payloads. The activity entails the exploitation of CVE-2023-48788 (CVSS score: 9.3), a critical SQL injection flaw that could permit an unauthenticated attacker to […]
Cloud-Native Application Protection Platform (CNAPP) , Data Loss Prevention (DLP) , Endpoint Security Data Security Posture Management Deal Will Help CrowdStrike Guard Endpoints, Clouds Michael Novinson (MichaelNovinson) • March 5, 2024 CrowdStrike plans to purchase a data security posture management startup led by an Israeli Defense Forces team leader to safeguard information across […]
Lift and shift migration involves moving an application and its associated data, OS and workload to a new environment — usually from on premises to the cloud. It provides a way to move apps without redesigning them to suit the new infrastructure or fundamentally changing the workload. Data center admins use lift and shift to […]
Cybercriminals are using a network of hired money mules in India using an Android-based application to orchestrate a massive money laundering scheme. The malicious application, called XHelper, is a “key tool for onboarding and managing these money mules,” CloudSEK researchers Sparsh Kulshrestha, Abhishek Mathew, and Santripti Bhujel said in a report. Details about the scam […]
Last year, the Open Worldwide Application Security Project (OWASP) published multiple versions of the “OWASP Top 10 For Large Language Models,” reaching a 1.0 document in August and a 1.1 document in October. These documents not only demonstrate the rapidly evolving nature of Large Language Models, but the evolving ways in which they can be […]
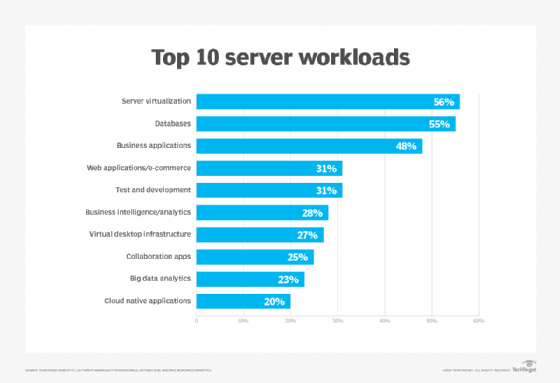
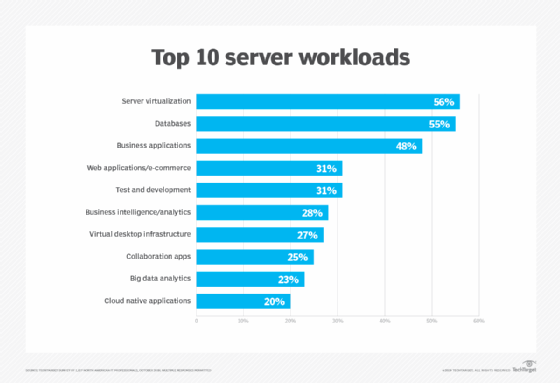
What is a workload? In computing, a workload is typically any program or application that runs on a computer. A workload can be a simple alarm clock or contact app running on a smartphone. Or it can be a complex enterprise application hosted on one or more servers with thousands of clients, or user systems […]
What is a workload? In computing, a workload is typically any program or application that runs on a computer. A workload can be a simple alarm clock or contact app running on a smartphone. Or it can be a complex enterprise application hosted on one or more servers with thousands of clients, or user systems […]
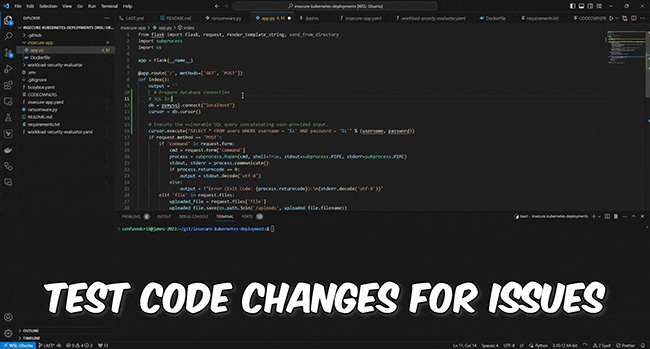
Latio Application Security Tester is an open-source tool that enables the usage of OpenAI to scan code from the CLI for security and health issues. Features and future plans James Berthoty, the creator of Latio Application Security Tester, told Help Net Security about the unique features that make it stand out: 1. Easily send code […]