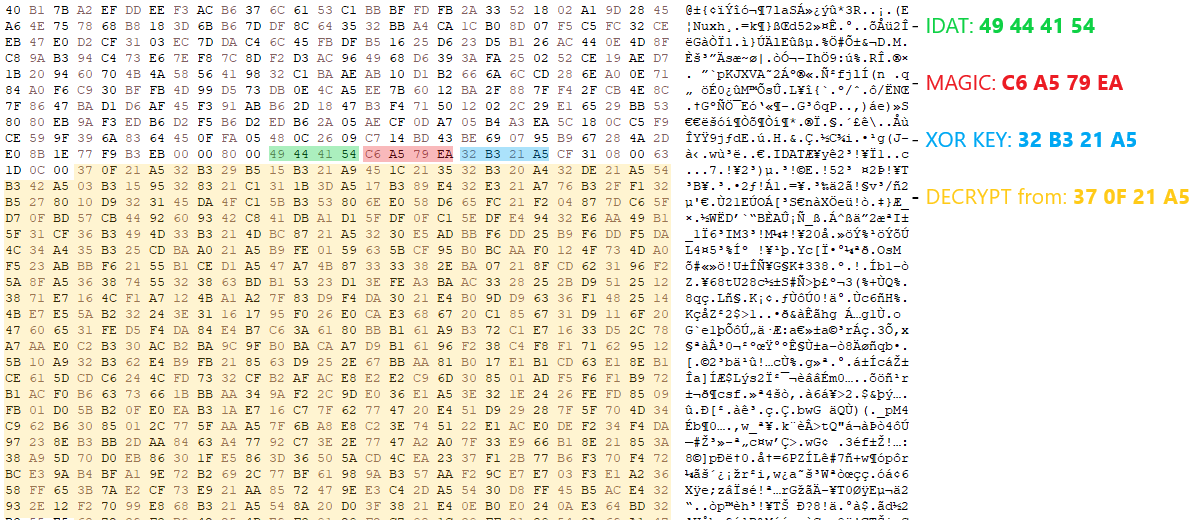
HijackLoader continues to become increasingly popular among adversaries for deploying additional payloads and tooling A recent HijackLoader variant employs sophisticated techniques to enhance its complexity and defense evasion CrowdStrike detects this new HijackLoader variant using machine learning and behavior-based detection capabilities CrowdStrike researchers have identified a HijackLoader (aka IDAT Loader) sample that employs sophisticated evasion […]
Citrix provides additional measures to address Citrix Bleed Pierluigi Paganini November 22, 2023 Citrix urges admins to kill NetScaler user sessions after patching their appliances against the CVE-2023-4966 Citrix Bleed vulnerability. Citrix is providing additional measures to admins who are patching their NetScaler appliances against the CVE-2023-4966 ‘Citrix Bleed‘ vulnerability. The company is urging admins […]
Advances in AI, IoT and high-performance computing drive the need for additional data center help. With these advances, customers and facility owners need a way to bring more capacity and power density to their data sources. There are two types of data centers: modular data centers (MDCs) and traditional data centers (TDCs). MDCs are economical, […]
Deduce has raised $9 million in funding led by Freestyle Capital, with additional investment by Foundry and True Ventures. The funding will launch Deduce’s GenAI Identity fraud solution out of stealth and help the company scale to prevent large-scale SuperSynthetic identity fraud across multiple verticals, including the financial service industry, fintech, and e-commerce. The rise […]
Dive Brief: Top cybersecurity officials from the Biden administration pledged additional support to the open source software community and private sector security executives during the Secure Open Source Software Summit in Washington D.C. Tuesday. The Cybersecurity and Infrastructure Security Agency released a roadmap for open source software security, which is designed to establish the agency’s role […]
⚠️ September 5, 2023: This appears to be an ongoing campaign with additional packages published. The package timeline table has been updated to reflect this. Phylum has been extremely busy in the past few weeks, reporting on multiple malware campaigns, including malicious updates to npm packages, malware masquerading as a GCC binary, and a package […]