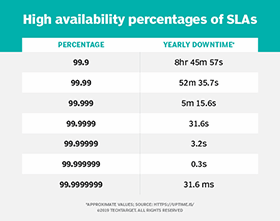
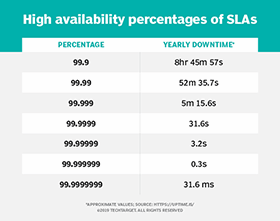
What is high availability (HA)? High availability (HA) is the ability of a system to operate continuously for a designated period of time even if components within the system fail. A highly available system meets an agreed-upon operational performance level by eliminating single points of failure. This is accomplished by including redundant components that serve […]
What is high availability (HA)? High availability (HA) is the ability of a system to operate continuously for a designated period of time even if components within the system fail. A highly available system meets an agreed-upon operational performance level by eliminating single points of failure. This is accomplished by including redundant components that serve […]
97% of office workers across the UK and US trust their cybersecurity team’s ability to prevent or minimize damage from cyberattacks, according to CybSafe. The study examining attitudes towards cybersecurity teams within organizations has uncovered that despite minor issues around communication and processes, there are high levels of trust and appreciation amongst employees. It indicates […]
You may have seen the news that in a recent Serato DJ update – the ability for Serato Stems to work with tracks streamed from TIDAL was removed. The music streaming service has also pulled access to Stems for DJs in new updates to Rekordbox DJ, Virtual DJ, djay Pro, and so on. Many DJs […]
Last updated 19 January, 2024 Real-time stems control – the ability to separate vocals from instrumentals instantly when DJing – is currently the cutting-edge battleground for DJ software manufacturers. It’s a fast-moving area, and many software makers are already onto their second or third iteration of stems in their software. So just like last year, […]
Modern security tools continue to improve in their ability to defend organizations’ networks and endpoints against cybercriminals. But the bad actors still occasionally find a way in. Security teams must be able to stop threats and restore normal operations as quickly as possible. That’s why it’s essential that these teams not only have the right […]
Modern security tools continue to improve in their ability to defend organizations’ networks and endpoints against cybercriminals. But the bad actors still occasionally find a way in. Security teams must be able to stop threats and restore normal operations as quickly as possible. That’s why it’s essential that these teams not only have the right […]
Oct 10, 2023NewsroomPassword Security / Technology Google on Tuesday announced the ability for all users to set up passkeys by default, five months after it rolled out support for the FIDO Alliance-backed passwordless standard for Google Accounts on all platforms. “This means the next time you sign in to your account, you’ll start seeing prompts […]
Linux certifications test your ability to deploy and configure a Linux system in a business context. These certifications range from vendor-specific to distribution-agnostic. Several certification vendors provide specialization paths that enable candidates to pursue specific skill sets that match their job roles. IT professionals use certifications to add to their resumes to prove their knowledge […]
- 1
- 2