Linux Version of DinodasRAT Spotted in Cyber Attacks Across Several Countries
A Linux version of a multi-platform backdoor called DinodasRAT has been detected in the wild targeting China, Taiwan, Turkey, and Uzbekistan, new findings from Kaspersky reveal.
DinodasRAT, also known as XDealer, is a C++-based malware that offers the ability to harvest a wide range of sensitive data from compromised hosts.
In October 2023, Slovak cybersecurity firm ESET revealed that a governmental entity in Guyana had been targeted as part of a cyber espionage campaign dubbed Operation Jacana to deploy the Windows version of the implant.
Then last week, Trend Micro detailed a threat activity cluster it tracks as Earth Krahang and which has shifted to using DinodasRAT since 2023 in its attacks aimed at several government entities worldwide.
The use of DinodasRAT has been attributed to various China-nexus threat actors, including LuoYu, once again reflecting the tool sharing prevalent among hacking crews identified as acting on behalf of the country.
Kaspersky said it discovered a Linux version of the malware (V10) in early October 2023. Evidence gathered so far shows that the first known variant (V7) dates back to July 2021. Check Point has since detected a next generation version (V11) in November 2023.
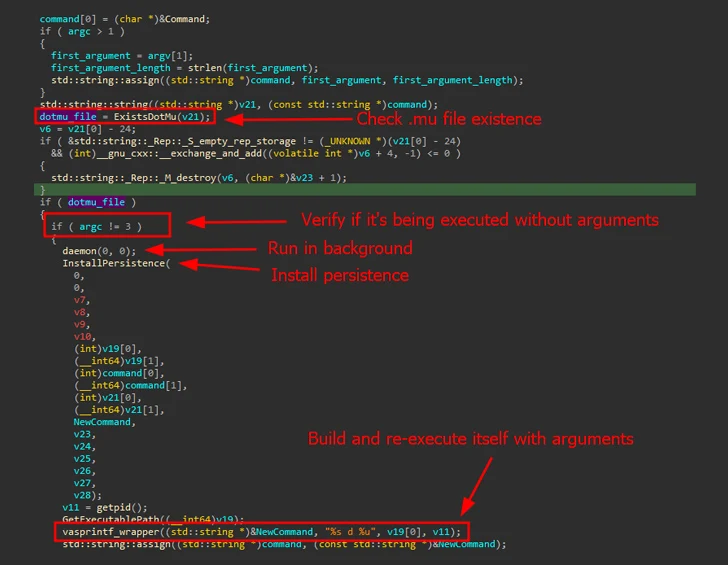
It’s mainly designed to target Red Hat-based distributions and Ubuntu Linux. Upon execution, it establishes persistence on the host by using SystemV or SystemD startup scripts and periodically contacts a remote server over TCP or UDP to fetch the commands to be run.
DinodasRAT is equipped to perform file operations, change command-and-control (C2) addresses, enumerate and terminate running processes, execute shell commands, download a new version of the backdoor, and even uninstall itself.
It also takes steps to evade detection by debugging and monitoring tools, and like its Windows counterpart, utilizes the Tiny Encryption Algorithm (TEA) to encrypt C2 communications.
“DinodasRAT’s primary use case is to gain and maintain access via Linux servers rather than reconnaissance,” Kaspersky said. “The backdoor is fully functional, granting the operator complete control over the infected machine, enabling data exfiltration and espionage.”
Check Point, in its own analysis of DinodasRAT, described the malware as initially based on an open-source project called SimpleRemoter, a remote access tool that has its foundation in the Gh0st RAT. The Israeli cybersecurity company is tracking the Linux variant under the name Linodas.
“The authors appear to be proficient in Linux, as their choice to support the OS was not just a simple #ifdef variant of a Windows RAT but a different project with a separate code base and possibly a different development team,” Check Point noted.
The latest version of backdoor further comes with capabilities to create multiple threads to perform system monitoring, download an additional module that can interfere with the functioning of certain binaries in the system, and remove reverse shell sessions that have been inactive for nearly an hour.
The primary purpose of the auxiliary module, called the filter module, is to act as a proxy the execution of original binary (e.g., who, netstat, and ps) and control its output, effectively allowing the threat actors to glean information from the host and better evade detection.
“The complexity and capabilities of Linodas highlight the continued emphasis by threat actors on targeting Linux servers both as a method for maintaining presence and as a pivot point within compromised networks,” Check Point said.
“This approach likely exploits the typically lower level of security protocols and solutions usually installed on Linux boxes, allowing the attackers to extend their foothold and remain undetected for longer periods.”
(The story was updated after publication to include more information about DinodasRAT published by Check Point Research on March 31, 2024.)